
Magnet + Grayshift: Continuing to Provide the Most Advanced Solution for Mobile Investigations
Over the past year and half, we’ve been extremely proud to count on Grayshift as a partner. In addition to being the only company they’ve trusted to integrate GrayKey directly into a product (Magnet AXIOM), we’ve had the great opportunity to sell GrayKey to customers around the world — providing customers with the most advanced solution for iOS investigations.
We have also had a great time co-presenting at various events over this time (both live and obviously now virtual), including our Magnet User Summit, Magnet Virtual Summit, and Virtually Together events, as well as Techno Security, National ICAC Conference, and various live webinars. We’ve been so happy to hear from customers and attendees that they’ve learned a lot from our sessions and managed to find news ways to get and analyze iOS evidence.
As we continue to progress our exclusive partnership, we wanted to take a moment to reiterate some of the ways you can use Magnet AXIOM and GrayKey together to get the most evidence out of your investigations. We will be sharing several blogs over the next few weeks highlighting these areas. For a more comprehensive how-to document, check out this blog from Trey Amick.
A Partnership That Demonstrates the Deepest Levels of Analysis
The technical partnership we have developed with Grayshift allows Magnet Forensics research, development, and training efforts to focus on supporting the deepest level analysis from devices accessed with GrayKey — including parsing and extracting data from GrayKey extractions.
Our R&D teams also collaborate directly with the development teams at Grayshift to truly understand the data that is parsed and presented. This helps us find critical insights in data acquired from images created by Grayshift tools. Our goal is to bring new artifacts and insights to the data extracted from encrypted mobile devices by Grayshift tools.
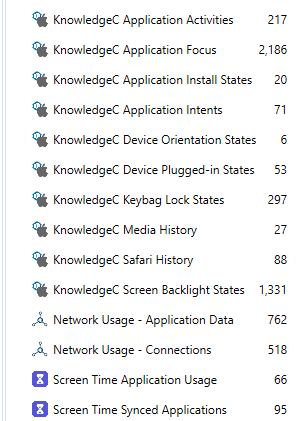
We also recognize the need for same day extractions provide by GrayKey. Through testing and research, we have discovered there are sensitive artifacts such as those found in Safari History, KnowledgeC, PowerLog, and ScreenTime. In order to parse the maximum results, you will need to acquire data as soon as possible. The GrayKey makes same day extractions from locked iOS devices a possibility. Without same day extractions, you may loose valuable data for your case. The combination of Magnet AXIOM + GrayKey allows digital forensic examiners to obtain relevant results from full content images that GrayKey provides.
Learn More About AXIOM & GrayKey in Our AX301 Course
As part of our relationship with GrayKey we offer MAGaK (Magnet AXIOM & GrayKey) Advanced iOS Examinations (AX301). This four-day course, available to law-enforcement agencies cleared by Grayshift, provides hands-on use of the GrayKey device and analysis of data from the acquired images.
In addition to using the GrayKey device to understand how to gain access to information previously unavailable by most forensic techniques, AX301 deep dives the artifacts core to the iOS file system. The class covers exclusive files system artifacts such as location history, third-party applications, and more. For those students who are looking for an advanced iOS analysis course, we offer Magnet AXIOM Advanced iOS Examinations (AX302) focusing on the same deep diving of iOS artifacts offered in AX301.
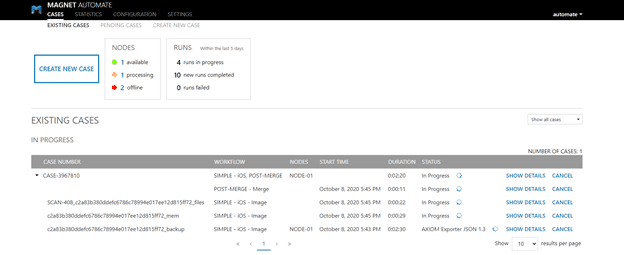
Use Magnet AUTOMATE to Orchestrate the Processing of GrayKey Images
If you are regularly creating mobile images with GrayKey, you can use AUTOMATE to orchestrate the process of analysis once the acquisition is complete. With the introduction of Watch Folders in AUTOMATE 2.2, the orchestration can take a completed GrayKey acquisition and process it with AXIOM, iLEAPP and other tools in your workflow such that you can start analysis as soon as processing is complete.
We hope to continue to bring collaboration, integration, and insights through the Magnet and Grayshift partnership. If you are interested in purchasing a GrayKey from Magnet Forensics, you can find out how here.
What further integrations would you like to see? Feel free to let me know at Jessica.Hyde@magnetforensics.com.
