Connecting Magnet AXIOM Directly to GrayKey for iOS Investigations
A lot of people using GrayKey for iOS extractions recognize the value it brings by allowing full access to the file system, bypassing passcodes, and gaining access to tons of data that would otherwise be unavailable to your investigation.
Magnet AXIOM is directly integrated with GrayKey, which allows the two tools to connect directly to each other, making the workflow even more seamless. You can launch AXIOM, connect to your GrayKey, and pull images directly into AXIOM for processing.
To learn more about the Connect to GrayKey workflow for Android, click here.
How to Connect to GrayKey in AXIOM
First, launch AXIOM and proceed to choose your evidence source by selecting Mobile -> iOS -> Connect to GrayKey

From there you’ll be prompted to input the hostname or IP address of your GrayKey box that is connected to the same network as your examination computer. You would have created this when you did the initial setup of the GrayKey device.
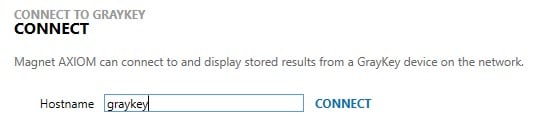
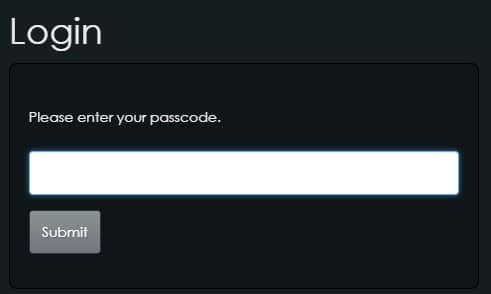
The last hostname/IP will be remembered if you have connected to the GrayKey previously. From there you will be prompted for the password for the GrayKey and if it’s the first time you’re connecting to it there will be an allow/deny screen authorizing Magnet AXIOM access to the GrayKey.
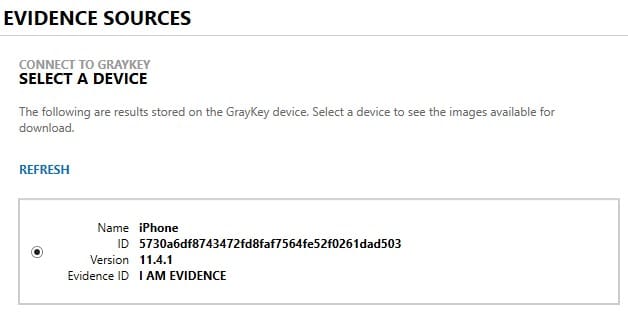
Once authenticated, you can choose a location where you want to store the GrayKey extractions. I’ll typically store this with the rest of my images on a separate drive but you can decide where is best for your workflow. Next, you’ll be presented with the list of extractions available to you on the GrayKey. The name, UUID, iOS version, and evidence ID are presented to identify which device you want to download.
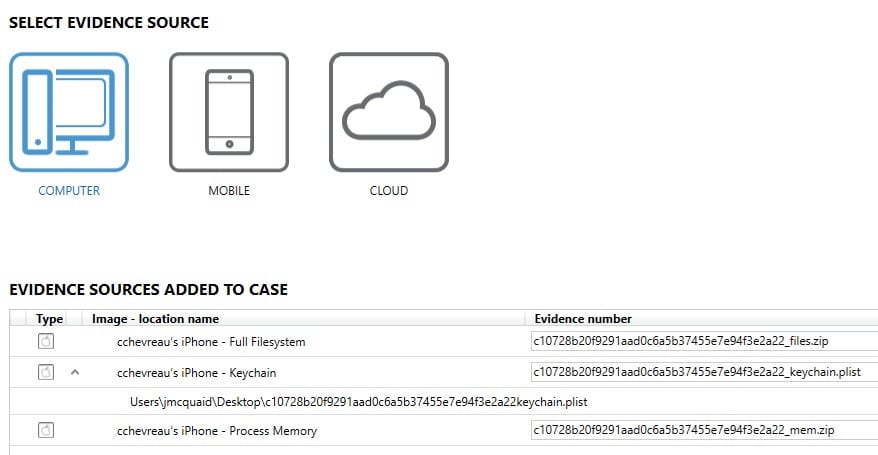
Once you have selected a device, the next screen will allow you to select what items you would like to process with AXIOM. The items available here will depend on the device and type of extraction performed but generally you’ll have the option to include a file system dump, the keychain, and process memory. You can also pre-process the keychain from GrayKey iOS extractions, learn more here.
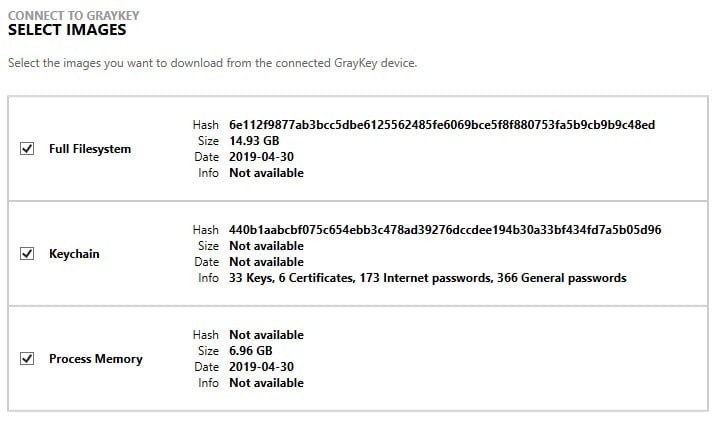
Once your options are selected, hit Next and your download will begin. Once the download is complete, AXIOM will automatically verify the hash of the file to validate that the download was completed successfully. If the download fails or the hash verification is incorrect, you will be given the option to retry the download.
After everything completes successfully, the evidence will be loaded into AXIOM and you can begin processing the evidence. This new integration will allow examiners to save time by integrating their two favorite tools together for iOS investigations. Additionally, it will help validate the integrity of the evidence that is being downloaded by verifying the image hashes.
