Loading iOS Full File System Images from GrayKey and Cellebrite into Magnet AXIOM
Getting iOS Full File System Images is crucial for digital investigators and examiners. For years, most forensic examinations of iOS devices were limited to data only available in an iTunes backup and only if you had the user’s passcode. Sure, you may have gotten the odd jailbroken device, but it typically didn’t matter whether you had a ten thousand-dollar commercial forensics tool or a free acquisition tool like Magnet ACQUIRE, you were getting the same thing: an iTunes backup / logical collection of files. If you didn’t have the user’s passcode, you weren’t getting anything, so a backup type of extraction was better than nothing.
Enter iOS Full File System images that are now extractable using GrayKey or Cellebrite Premium. These tools can often extract the entire file system of an iOS device, even without having the passcode. This not only has provided examiners with access to devices that were previously inaccessible due to not having the passcode, but also gave them access to iOS data that hasn’t been available in years due to the limited data available via logical collections. In many cases, iOS Full File System images have revealed data we’ve never had the opportunity to investigate before!
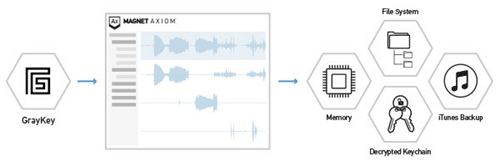
The good news is that Magnet AXIOM can ingest these more comprehensive extractions allowing examiners to analyze all this data. The actual files may vary depending on the tool used for acquisition.
GrayKey Acquisitions
Data acquired via a GrayKey extraction may be outputted into a variety of containers (Full Files, mem, and / or a plist).
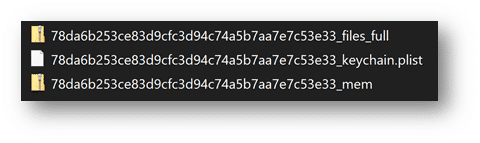
For investigators, the ideal GrayKey image you want when examining an iOS device is the files_full.zip. This has the entire iOS file system present and provides the maximum amount of information for examiners to use in the course of their examination.
Depending on the type of extraction (BFU, AFU), a mem.zip may also be generated for the device’s memory. This is a process memory dump of the iOS device. Prior to Grayshift’s technology, examiners hadn’t acquired process memory of iOS devices for routine analysis. The iOS process memory contains valuable information and should most certainly be loaded into AXIOM as well. A keychain.plist will most likely be generated with GrayKey. Most examiners are familiar with the iOS keychain as it contains the user accounts, passwords, and keys for many of the apps that the user has saved or used which can also be valuable for investigators wanting to authenticate to cloud sources or otherwise. The keychain that GrayKey creates is slightly different than the one you would get in an iTunes backup or found natively on a jailbroken device. The keychain found in the file system is actually a SQLite database and hasn’t always been available due to limitations in acquisitions prior to this. The keychain in an iTunes backup is also a plist but is formatted differently so we’ve added specific support for the GrayKey keychain.plist in Magnet AXIOM.
GrayKey will also produce a passwords.txt and a PDF report of the device extraction. While the passwords.txt list is great for examiners to look through, make sure to load the keychain.plist into AXIOM for parsing, not the passwords.txt file.
Cellebrite Acquisitions
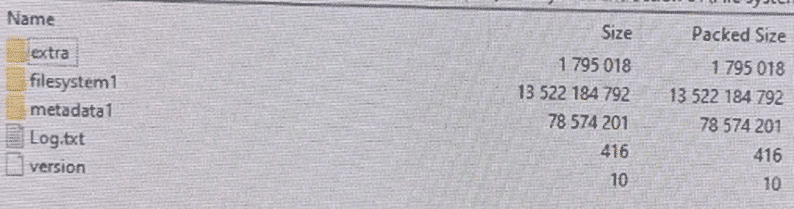
Data acquired using Cellebrite Premium may vary depending on the type of extraction achieved (hot, cold), the device model and / or iOS version. It may have a ufdx file, a Deviceinfo.txt file and folder for the iOS Full File system images.
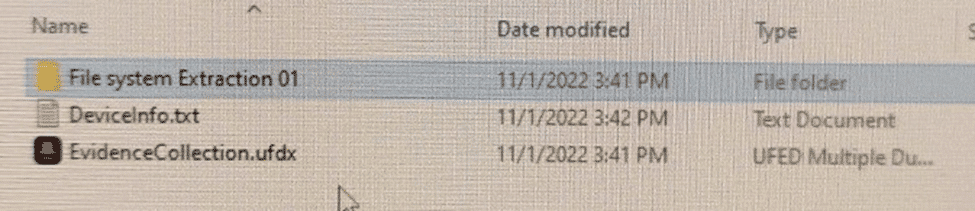
The File system Extraction folder contains a ufd file, as well as a File system Extraction.zip file.
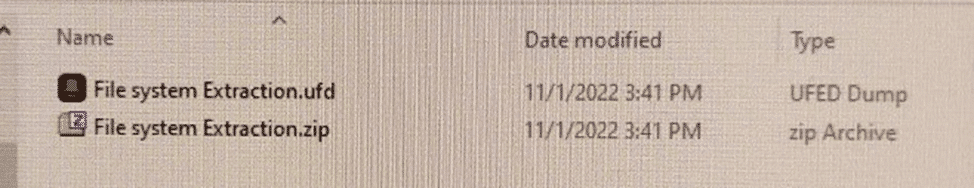
Within the File system Extraction.zip file, there are additional subfolders with one in particular to note – filesystem1. Within filesystem1, there is a keychain.plist.
Now that we’ve highlighted different exports examiners get from utilizing a GrayKey or Cellebrite Premium in their acquisition phase of their iOS investigation, let’s dive into analyzing this data with Magnet AXIOM.
**Note that no matter the tool used for the extraction, the keychain.plist may be embedded within another file. For example, a GrayKey extraction may save the keychain within a zip file or Cellebrite Premium may embed the keychain within a CBLX file. Magnet AXIOM will locate embedded keychains during processing for further analysis.
Now that we’ve highlighted different exports examiners get from utilizing a GrayKey in their acquisition phase of their iOS investigation, let’s dive into analyzing this data with Magnet AXIOM.
Loading iOS Full File System Images into AXIOM
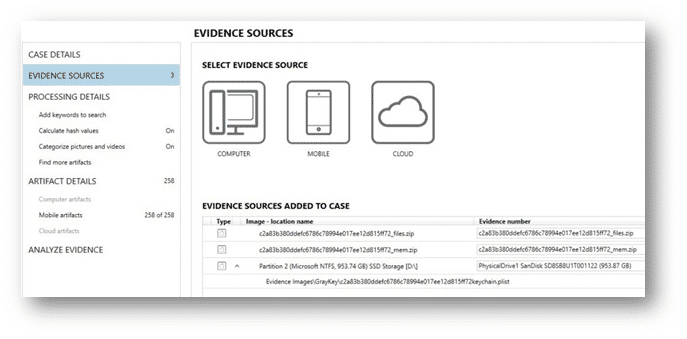
There are several ways to load your full file system extraction into Magnet AXIOM. Depending on the method of acquisition and how it was packaged by GrayKey or Cellebrite Premium, the process for loading the extraction in Magnet AXIOM may vary.
Loading full file system images into AXIOM may vary depending on the various proprietary methods of the tool used. You can follow the same path as most other iOS images by going Mobile -> iOS -> Load Evidence -> Image and then choosing the zip files. For GrayKey extractions, select the files.zip first, then the mem.zip in the same manner. For Cellebrite images, you may have a .ufd, ufdx or cblx file to select.
It’s important to note, make sure you select “Image” versus file and folder when loading in the files.zip. This will allow AXIOM to parse / carve the maximum amount of information out of the image.
You will be prompted to load the Keychain.
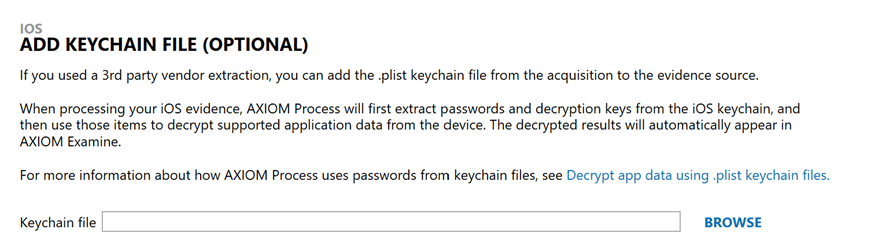
Another option is to load the keychain.plist first to see what credentials it may hold:
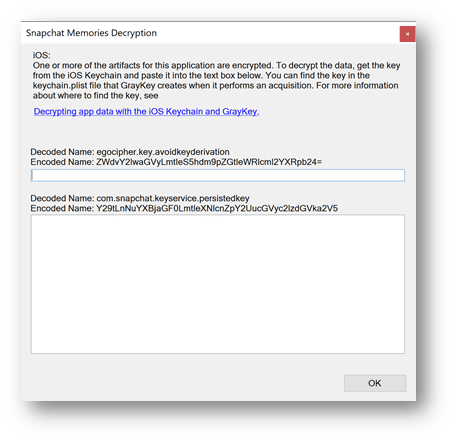
When dealing with iOS devices that you have the keychain.plist for, it may be beneficial for the examiner to process just the keychain and to review the data of that sole piece of evidence before navigating to the Case Dashboard of AXIOM Examine and hitting “Add Evidence”. Why you ask? Great question! By reviewing the keychain.plist, they will have a good idea of the apps that may be found on the suspect device. Better yet, when they load the files.zip into AXIOM for processing, they can supply potential passwords and key values for encrypted apps like SnapChat, WickrMe, or iOS Notes, so that during processing AXIOM can decrypt these databases for the examiner to analyze during the course of their investigation, without the need of having to re-process the evidence. We’ve added information within the artifact selection category for apps that we can decrypt during processing for examiners to reference when copying information out of the keychain into AXIOM, as seen below.
We can add additional evidence files into the already processed keychain.plist in Magnet AXIOM if the keychain is processed initially.
For agencies with an online GrayKey there is an additional option when it comes to loading your acquisitions into AXIOM. In conjunction with Magnet’s partnership with Grayshift, we have a direct connection which allows examiners to connect AXIOM directly to their GrayKey via a network connection. This direct-connect option has several benefits over the traditional procedure of downloading the images via a browser from your GrayKey before starting a case with your analysis software. The first benefit of using the direct connect option is speed; using this procedure reduces the steps needed to start your investigation overall, and when it comes to the volume of iOS devices you’ve acquiring, this time savings can really mount up. Secondly, AXIOM will prompt you on where to save the GrayKey image too as its acquired and processed for examination. As a part of this process we will also automatically hash the files we are acquiring, so that you can quickly confirm from the GrayKey GUI your hash values match. On numerous occasions we’ve heard investigators say that when they loaded their GrayKey image into their analysis tool, things seemed “off”, or the image couldn’t be loaded. This is in part to potentially the browser capping the size of the download, or a packet dropping during the download of the image file.
To load evidence via the direct connect method, users will go Mobile -> iOS -> Connect to GrayKey. Once connected, examiners can browser the available data that’s saved on the GrayKey, selecting the different evidence files they wish to acquire and process with AXIOM.
Once loaded you can choose whatever options and artifacts you wish to include in AXIOM for your given investigation. One feature that may help get additional data that otherwise wouldn’t be included in an artifact is the Dynamic App Finder (DAF).
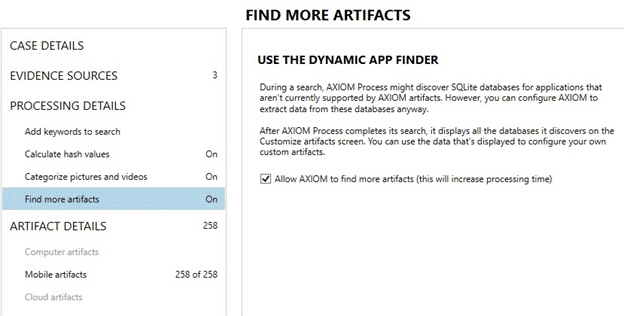
Under “Find more artifacts”, you can enable DAF and it will automatically search through the image for SQLite databases that may contain potential chat, geolocation, or contact information. This can be helpful for any applications or data that can’t already be found in an existing artifact. A quick video on DAF can be found here. For GrayKey images, this will identify additional data in the file system and memory images. You can find more information on creating custom artifacts and learning more about our Artifact Exchange here.
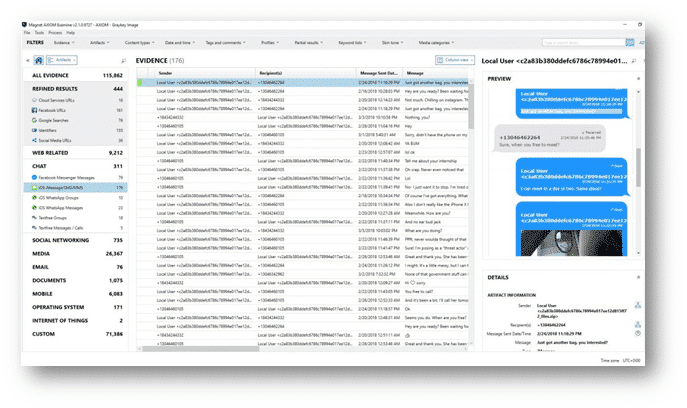
Once everything is loaded and options are selected, you can process the case just like any other and view the results in AXIOM Examine.
Want to learn even more about how you can use GrayKey and AXIOM together to maximize your iOS investigations? Check out our MAGaK (Magnet AXIOM & GrayKey) Advanced iOS Examinations (AX301) course!
