Mobile Device Artifacts: Exploring Geolocation, Communication, Application and Media Evidence
Mobile device artifacts have grown in importance as cell phones have become an integral part of everyday life (so much so that you can see many videos on social media where users are so engrossed in their devices that they walk into a fountain, bushes, or even traffic!) As entertaining as these videos can be, mobile devices are often connected to many crimes. In speaking with numerous law enforcement agencies, examiners have mentioned that mobile devices are present in most cases. Digital forensic labs at some agencies report that 90% of the devices they receive in connection to criminal investigations are mobile devices.
The corporate world is not exempt from the proliferation of mobile devices involved in investigations. Bring Your Own Device (BYOD) is prevalent in the corporate environment. Unfortunately, some employees may also be involved in illegal acts. Intellectual property theft, employee misconduct, or criminal acts may require examining mobile device artifacts.
What Are Mobile Device Artifacts?
Mobile device artifacts are digital breadcrumbs: forensically valuable data created by a mobile device that help investigators better understand a case. A mobile device can tell you where a person is at a given time. It can tell who they have been communicating with through artifacts from chat messages and call logs. Additionally, you may be able to recover emails that have been sent and received, which remain on the device. You will likely find images that have been taken with one of the onboard cameras or videos that have been created. Device usage statistics will tell when the phone was in use, and you can determine what apps were being used – a life analysis pattern can help refute claims that a user was asleep by showing they were interacting with an application on the device during a particular time frame.
How to Use Mobile Device Artifacts
When examining a mobile device, the specifics may vary in any given case. Still, typically examiners are interested in answering as many of the Who, What, When, Where, Why, and How questions as possible. The data on modern mobile devices can go a long way to answering these questions. We can use known artifacts specific to Android and iOS devices to help determine who a device user has been communicating with or where that device (and, almost by extension – the device user) has been. There are exceptions but consider your own smartphone usage habits. For many, it is one of the first things we look at in the morning and the last thing we look at before drifting off to sleep. Many people sleep with their smartphone on the nightstand beside their bed and use it to replace their alarm clock. Regardless of case type, the individuals connected to our investigations are no different. As examiners, we have all seen the value of mobile device data.
This study from Asurion conducted in 2022 shows that Americans check their phones 352 times per day! While this study is focused on US-based users, that behavior likely holds for users in the rest of the world. With mobile device use being such a regular part of everyday life, it’s no surprise that, as examiners, we would seek to use the data contained on those devices – and their applications and connected cloud accounts – to help corroborate our theory of what may have transpired during an investigation.
Top 5 Mobile Device Artifacts
Magnet Forensics has curated a list of the top five mobile device artifacts and where they can be found on a given device. Magnet AXIOM and AXIOM Cyber will surface these artifacts for you quickly and easily, and Magnet GRAYKEY and VERAKEY provide same-day access to the latest iOS and Android devices; but it’s important you know where to look:
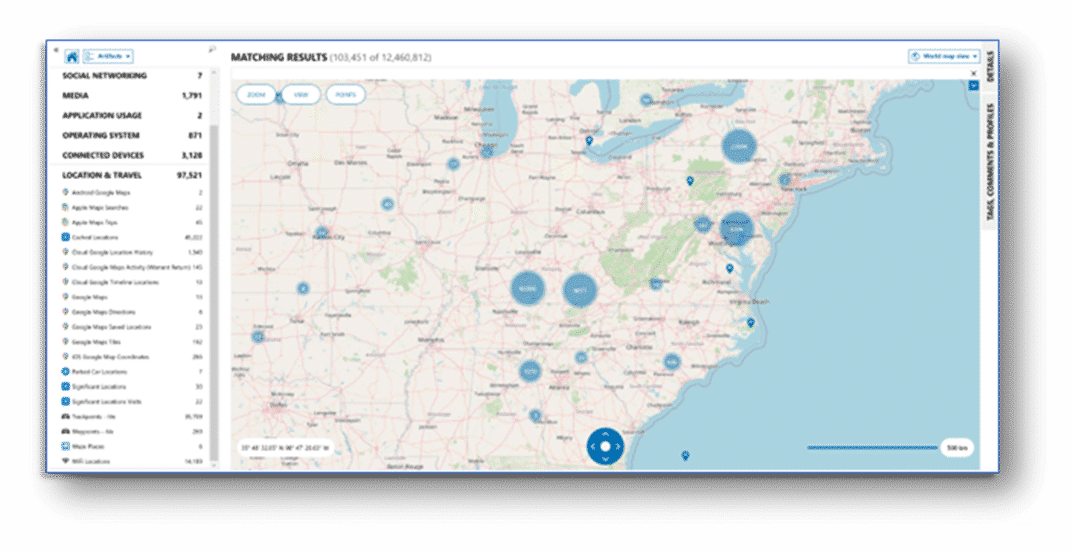
1. Geolocation artifacts
When individuals use apps, engage in calls, or connect to Wi-Fi networks, their devices record and store data that can be used to trace their movements. This information—like GPS data, cell tower connections, and timestamps—can help investigators piece together timelines and reconstruct events.
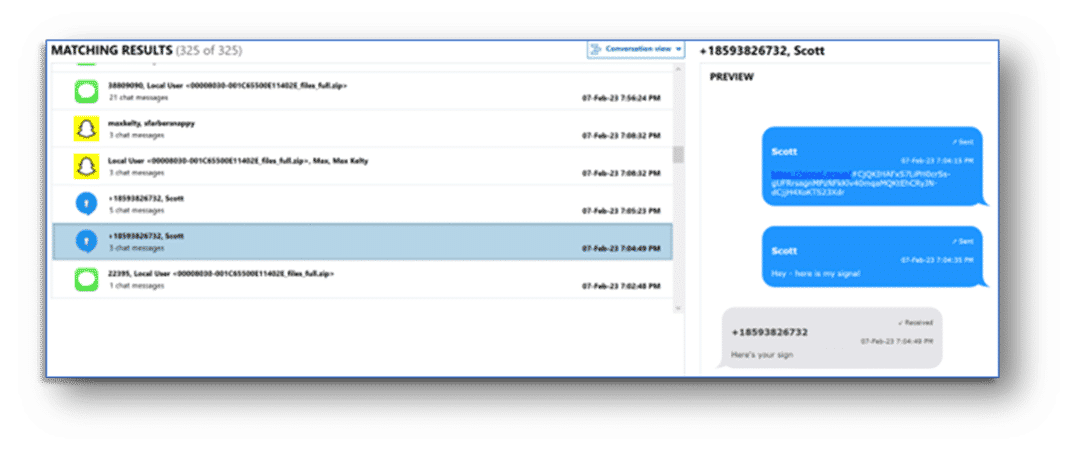
2. Communication Artifacts
Communication artifacts encompass a wide range of digital traces left behind by individuals as they engage in various forms of communication through their mobile devices. These artifacts can include text messages, call logs, emails, instant messaging posts, and more.
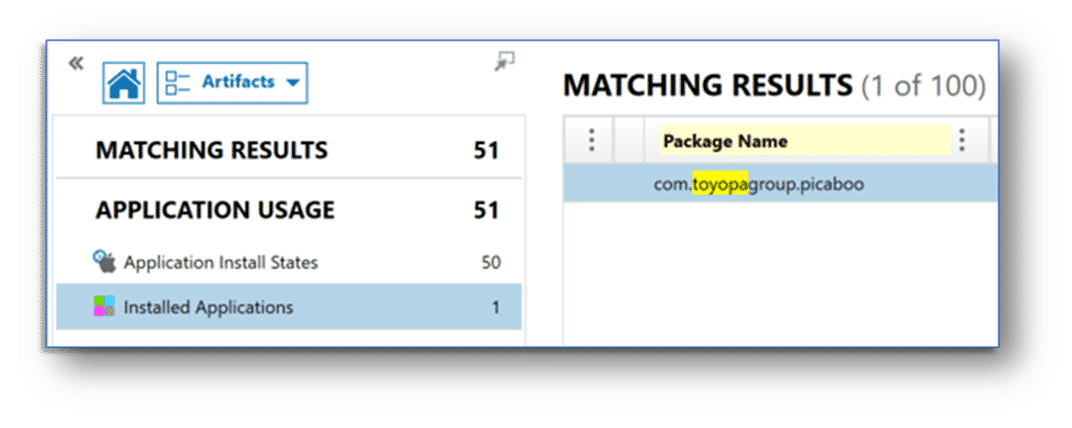
3. Application Artifacts
Application artifacts provide a glimpse into an individual’s digital life, offering insights into their activities, preferences, and connections. In mobile device investigations, application artifacts can be indispensable tools for reconstructing narratives, understanding behaviors, and ultimately uncovering the truth.
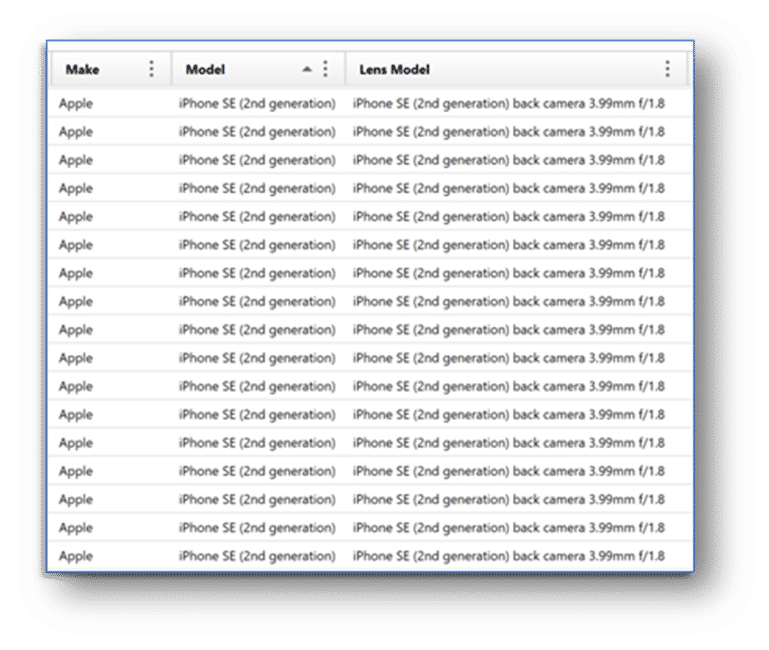
4. Media Artifacts
Media artifacts serve as windows into a suspect’s experiences, interactions, and surroundings. These artifacts can prove essential for reconstructing events, corroborating statements, and painting a vivid picture of the truth.
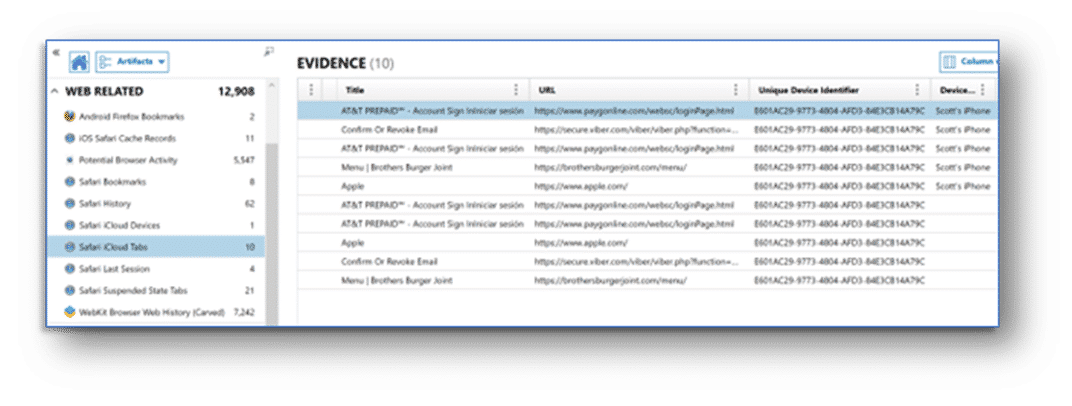
5. Web Browser Activity Artifacts
Web browser activity artifacts provide a virtual breadcrumb trail for an investigator to follow into a suspect’s online world. Browsing history, search queries, bookmarks, cached data, and downloaded files can all leave footprints that prove useful to follow in a mobile device investigation.