How to Uncover Web Browser Activity Artifacts for Mobile Device Investigations
Web browser activity artifacts are digital clues suspects create when they use web browsers on mobile devices. Browser history, cookies, cache, and file downloads are all web activity artifacts that investigators may find useful during a mobile device investigation.
Knowing which browsers are installed, along with their specific artifacts, can be great information to have in any investigation. While we’ve come to expect things like Safari-related artifacts on an iOS device, Apple has (in more recent iOS releases) made it possible to change the default browser.
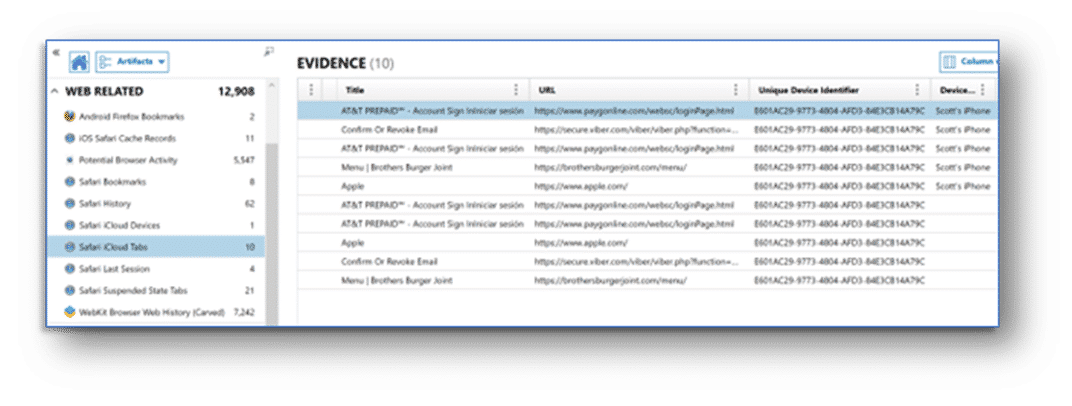
It’s worth noting that some device users may engage in compartmentalization here, as well. Using something like Mozilla Firefox for their day-to-day browsing and Google Chrome for other activities. With both Android and iOS mobile operating systems, there are mechanisms in place to provide the user with a continuity of service across their devices. This means that iOS devices may have additional web related artifacts outside of the typical Safari Web History, like the Safari iCloud tabs artifact category. Similarly, Android device users browsing with Chrome may be synchronizing their data to an associated Google account.
Files saved from the web may be on the device and artifacts associated with the file management application may help to track them down, or web-related artifacts showing downloads may help. Additionally, because of traditional on-device storage limitations associated with mobile devices, the connected cloud accounts may contain any downloaded files.
Top Web Browser Activity Artifacts for Android and iOS
Magnet Forensics has curated the following list of top web browser activity artifacts and where they can be found on a given device. Magnet AXIOM and AXIOM Cyber will surface these artifacts for you quickly and easily, and Magnet GRAYKEY and VERAKEY provide same-day access to the latest iOS and Android devices; but it’s important you know where to look:
Android Web Activity Artifacts
| Chrome Browser Data |
| /data/data/com.android.chrome/app_chrome/Default/Web Data |
| /data/data/com.android.chrome/app_chrome/Default/Cookies |
| /data/data/com.android.chrome/app_chrome/Default/Favicons |
| /data/data/com.android.chrome/app_chrome/Default/History |
| /data/data/com.android.chrome/cache/Cache/ |
| /data/data/com.android.chrome/app_chrome/Default/Top Sites |
| /data/data/com.android.chrome/app_chrome/Default/Sync Data/SyncData.sqlite3 |
| /data/data/com.android.chrome/app_tabs/custom_tabs/ |
| /data/data/com.google.android.captiveportallogin/app_webview/Default/Cookies |
| /data/com.android.browser/browser.db/dbdata/databases/com.android.browser/browser.db |
iOS Web Activity Artifacts
| Safari Browser Data |
| /private/var/mobile/Library/History.db |
| HomeDomain-Library/Sarfary/History.db |
| /private/var/mobile/Library/Safari/CloudTabs.db |
| /private/var/mobile/Containers/Data/Application/[APPGUID]/Library/Safari/Downloads/Downloads.plist |
| AppDomain-com.apple.mobilesafari/Library/Safari/Downloads/Downloads.plist |
Leveraging Web Activity Artifacts
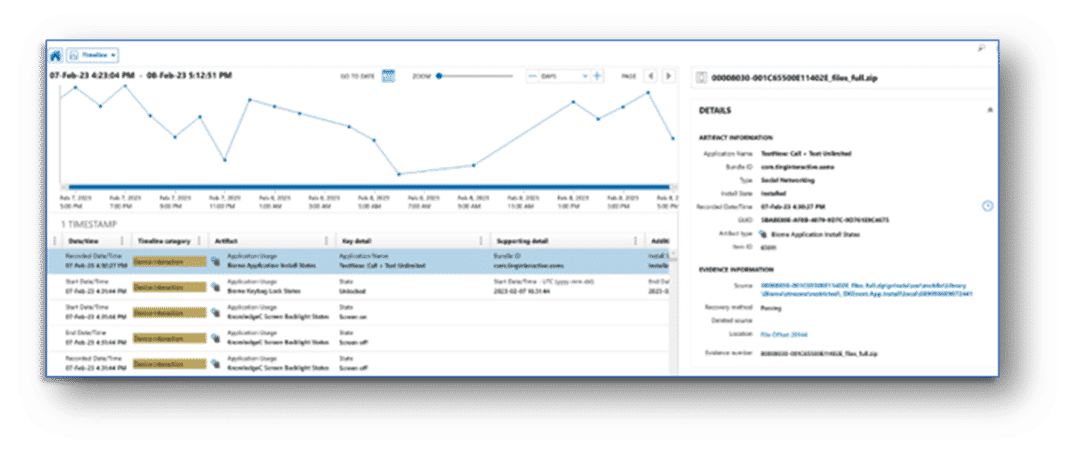
While many examiners spend the bulk of their time using the artifact explorer in AXIOM Examine, other features like Timeline and Connections can help surface items of interest. The volume of artifacts from a modern mobile device examination can make it easy for potential web activity artifacts to blend into the noise, almost hiding in plain sight.
Using the Timeline explorer can help to profile when a particular activity occurred on a device or provide context as to what a user was doing on their device at a certain time. The use of absolute and relative time filters can also help examiners find key details around points of interest in the timeline of a specific investigation.
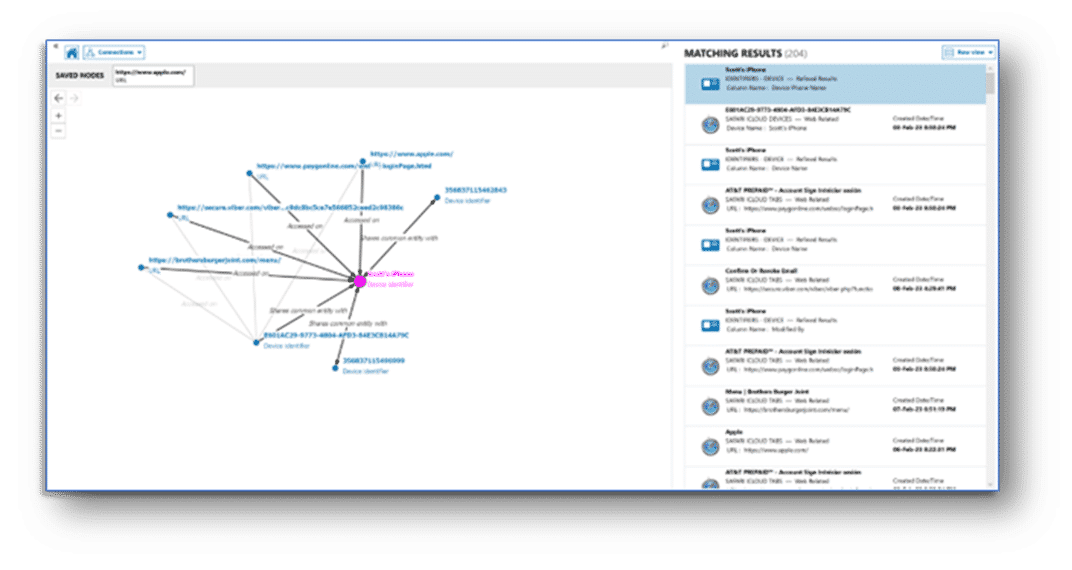
The connections explorer provides a visual representation of how the various artifacts in your case are related. By using the distinct properties of each artifact, called artifact attributes, you can show relationships between an artifact of your choosing – such as a screen name or phone number – to see how they relate to web activity artifacts and downloaded files of interest in your case.
These days, mobile devices often have greater storage capacity, even rivaling traditional computers. Still, the always-on, always-connected nature of mobile devices means that cloud stored data cannot be overlooked. The Potential Cloud Evidence Leads dashboard is a great resource for identifying other sources of data which may be relevant to your investigation – particularly when mobile devices are involved.
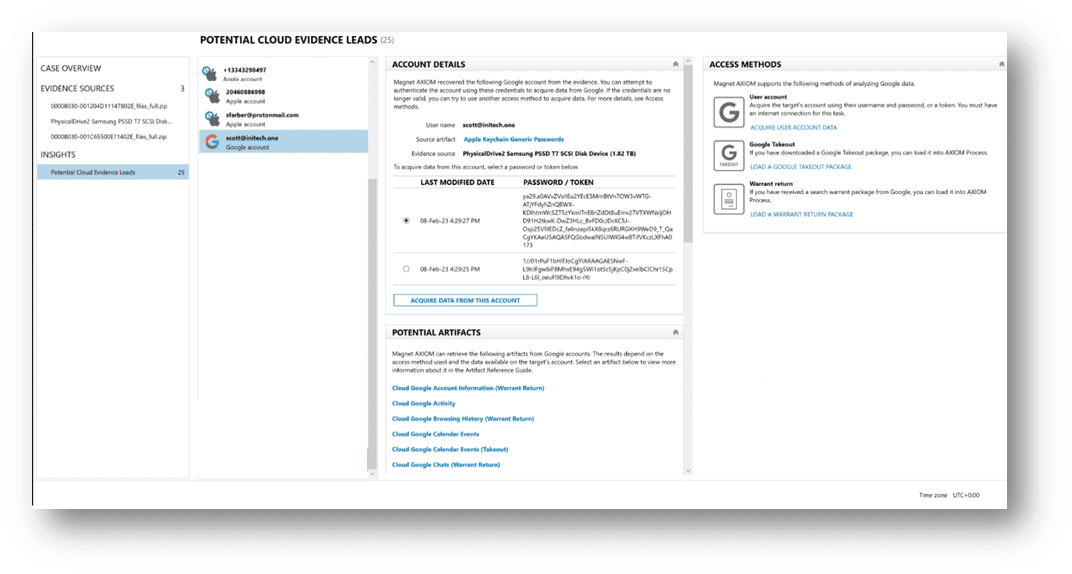
Applications on a device may not always store data locally or there may be additional logs, usage, and analytics data available directly from the connected cloud account. The potential cloud evidence leads dashboard helps examiners by surfacing potential sources of cloud-stored data and accounts from the installed applications and accounts recovered on a device. This can help to provide an efficient method for directing further investigative efforts in a case.
If you haven’t tried Magnet AXIOM or AXIOM Cyber, request a free trial today.
