How Are You Preparing Your Lab for Chromebook Acquisition and Analysis?
Is 2021 going to see continued growth for Chromebooks? Early indicators are trending that way. And with the rise of the Chromebooks, digital investigations have the potential to become much more complex because Chromebooks require a device plus cloud-centric approach, which can put pressure on digital forensics labs.
In this blog, we will provide some background information, resources, and tools to help you prepare for Chromebook investigations.
You can also learn more about Chromebook Analysis by checking out Jessica Hyde’s Magnet Virtual Summit webinar, Taking a Byte of Chromebook Analysis.
Chrome OS Market Share: It’s on the Rise
The global pandemic and the significant boost in online learning appear to have catalyzed demand for Chromebooks. In 2020, Chromebooks nearly tripled their quarterly sales based on market share (devices sold with Chrome OS jumped from 5.3% of market share in Q1 to 14.4% in Q4). Windows OS is still in the pole position, but computers powered by both Chrome OS and macOS made significant gains in market share, eating into Windows’ market dominance.1 Chromebooks also outsold Macs for the first time in 2020 and the trend doesn’t appear to be reversing in the near-term.2
Based on the early indicators for Q1, 2021 Chromebooks may also be displacing some tablet sales.3 No matter how you slice it, Chromebooks are on a high-growth trajectory, and with more Chromebooks in circulation increasing demand for Chromebook investigations likely won’t be far behind.
What’s Different About Chromebooks?
Do Chromebooks really pose a unique challenge for examiners?
The short answer is, yes. The long answer is still yes, but the challenge really comes in the form of complexity per device, such as the extra steps needed to prepare for a Chromebook acquisition, plus the multiple cloud-account investigation that Chromebooks are likely to necessitate.4 Compared to traditional laptops, low-cost Chromebooks, such as the Samsung Chromebook 4 (Intel® Celeron 4000 processor, 4GB Ram, 32GB SSD), are designed to run a lightweight OS at reduced cost while increasing grab-and-go portability.5 To get the desired result, these Chromebooks store the majority of user data in the cloud.
Chromebooks, though, can’t all be treated equally. Google offers the premium Pixelbook Go (8th Gen Intel® CoreTM I7 processor, 16GB RAM, 256GB SSD), for example, which is commonly compared to a Macbook Air for tech review blogs.6 In both cases (low-cost and premium), a device plus cloud accounts approach would be beneficial, but the premium Chromebook will likely have more data stored on the device in addition to the cloud data. Either way, there may be unique data on the device itself, such as extensions and downloaded items for offline work.
The Challenge of Chrome OS
One of the other aspects that makes Chromebook investigations challenging is that Chrome OS is hosted on specifically optimized hardware to enhance performance and security. Chrome OS automatically updates to the latest version to ensure security is maintained, heading off exploitable vulnerabilities. Chrome OS and its auto-updates should not be confused with Chromium OS, where users are responsible for manually updating the OS, and therefore may be more vulnerable to exploits.
What is Chromium OS? It’s an open-source equivalent of Chrome OS that can be run on any machine. It’s an appealing alternative for many users interested in Chrome OS. To get Chrome OS, you must purchase a Chromebook (with the optimized hardware); you can’t buy Chrome OS off the shelf and install it on another machine. So, if users want a Chrome OS experience, but don’t want to buy a Chromebook, Chromium is an option. Chromium OS users are likely to be more advanced and examiners may see these users running Chromium virtual machines or a custom home brew setup.
Making Sense of Fragmented Data
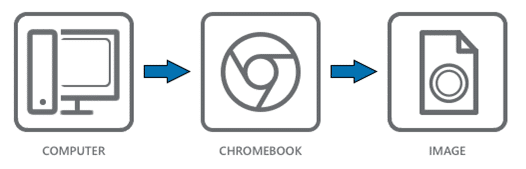
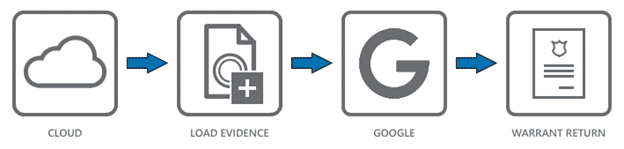
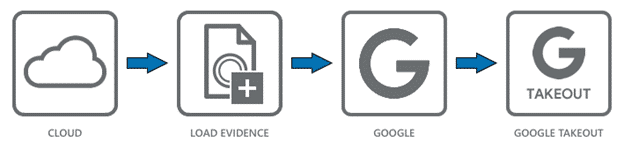
Imaging a Chromebook’s drive, effectively, is only one piece of a much larger, fragmented, decentralized puzzle when acquiring a single user’s data. Due to the design of Chromebook data management, it can put pressure on labs because processing the data from a Chromebook image is just a starting point. On top of imaging a Chromebook’s drive, examiners will also have to obtain a warrant return or a Google Takeout (via consent with credentials) along with it. Plus, if there are multiple users using a Chromebook, examiners will likely want to acquire the credentials and cloud accounts for each user.
Further complicating matters is that if Chromebooks aren’t in developer mode – which is unusual, they require username and password credentials before acquisition can occur. A Chromebook can be placed in developer mode at any time, but in doing so the user data is erased.7 Keep an eye out for Chromebooks in developer mode, because it likely suggests a more advanced user. Developer mode gives a user the ability to tweak and tinker with their device, so they can sideload Android apps or Bootstrap Chrome extensions.
Preparing for Chromebook investigations, then also means preparing for image acquisition in multiple ways, including requesting users to disclose their username and password, applying for a warrant, or having users download their data for analysis (e.g., Google Takeout feature).
To learn more about acquiring Google user data, check out their FAQ.
‘Hardware Plus Cloud’ the New Norm?
There are a few challenges in Chromebook investigations: greater emphasis on cloud-centric investigations, more evidence sources to manage per investigation, and more layers of security to bypass that may require either user disclosure of credentials or warrant returns if you’re in North America.
As more Chromebooks enter the market, it’s just another tool to be leveraged and/or exploited in criminal activity, but it’s a tool that adds an extra layer of complexity when unearthing evidence. For a lightweight, relatively inexpensive piece of hardware, Chromebooks really do have the potential to increase investigation timelines.
We may also see this trend expand beyond Chromebooks to standard laptops. Grab-and-go portability is unlikely to decrease in demand, so ‘hardware plus cloud’ investigations will likely become more of the new norm.
As more users host data in the cloud, there will be more pressure to collect user credentials (usernames, passwords, emails, phone numbers, etc.) but, it also likely means an increasing number of user-account data downloads and/or warrant returns. It’s important to note that Google warrant returns and Takeouts will include data from multiple devices in the account (phones, PCs, etc.), not just the Chromebook. With Magnet AXIOM, though, analyzing warrant returns and managing multiple evidence sources is easy.
Read more about how AXIOM makes analyzing warrant returns easy in Jessica Hyde’s blog series.
Resources for Chromebook Investigations
To help address the challenges of Chromebook acquisition, image processing, and analysis, there are a few resources and tools from Magnet Forensics that can help.
We recently released a free tool, the Magnet Chromebook Acquisition Assistant, which helps to automate the Chromebook acquisition methods developed by Daniel Dickerman. Once an image has been acquired, Magnet AXIOM has dedicated Chromebook artifact support, which was introduced in AXIOM 4.11.
Chromebook investigations also require some unique workflows to solve them. Jessica Hyde is our resident Chromebook expert here at Magnet Forensics and she’s generated several training and investigation resources for examiners:
- A quick reference guide for popular Chromebook data locations
- “Google Warrant Returns in Magnet AXIOM” — A blog post where you will learn more about unpacking Google Warrant Returns
- A Chromebook Acquisition Assistant Tip and Tricks webinar
Chromebook data extraction is garnering a lot attention in the broader community. Mark Mackinnon has recently developed an open source Chromebook processing tool in Python 3: ChromeOS Logs Events And Protobuf Parser (CLEAPP). CLEAPP is based on the Android Logs Events And Protobuf Parser community project. You can read about and download the tool here in Alexis Brigoni’s blog: “CLEAPP it! – ChromeOS Logs Events And Protobuf Parser.“
Analyzing a Chromebook image is likely to be just one evidence source in the investigation. With AXIOM examiners can easily manage the broader case needs by processing Chromebook images, alongside mobile, computer, cloud images, user-account data downloads, and warrant returns with dedicated artifact support all in one case.
Prepare your lab for Chromebook investigations with Magnet AXIOM. If you haven’t tried AXIOM or AXIOM Cyber yet, request a free trial here.
- Windows OS isn’t going to be displaced as the incumbent anytime soon, but from Q1 to Q4 of 2020 devices running Windows OS dropped from 87.5% to 76.7% of market share for new device sales. Chromebooks on the other hand grew from 5.3% of new sales in Q1 to 14.4% by Q4. Those numbers are huge. Chromebook quarterly market share for new device sales nearly tripled over the course of 2020. What’s even more impressive about the Chromebook trend is that Chromebooks doubled the Q4 performance of Mac sales, which hovered at 7.7%.
- https://www.geekwire.com/2021/chromebooks-outsold-macs-worldwide-2020-cutting-windows-market-share/
- https://www.idc.com/getdoc.jsp?containerId=prUS47648021
- To acquire a Chromebook image, three 32GB USB drives, plus an external hard drive large enough to make a copy of the Chromebooks hard drive is required. To read more about what’s unique to Chromebook imaging, refer to Daniel Dickerman’s Chromebook acquisition method.
- $299 US for base model Samsung Chromebook 4 (Intel® Celeron 4000 processor, 4GB Ram, 32GB SSD) as of May 10, 2021.
- $1399US for premium model Pixelbook GO (8th Gen Intel® CoreTM I7 processor, 16GB RAM, 256GB SSD) as of May 10, 2021.
- https://support.google.com/chrome/a/answer/1360642?hl=en
