Collecting Box.com Activity in Magnet AXIOM Cyber
With the continued trend towards remote work and dispersed workforces, companies are increasingly turning to cloud services for file storage, management and collaboration. Providing the storage for over 100,000 organizations and 67% of Fortune 500, Box.com has emerged as one of the leading cloud storage solutions for businesses.
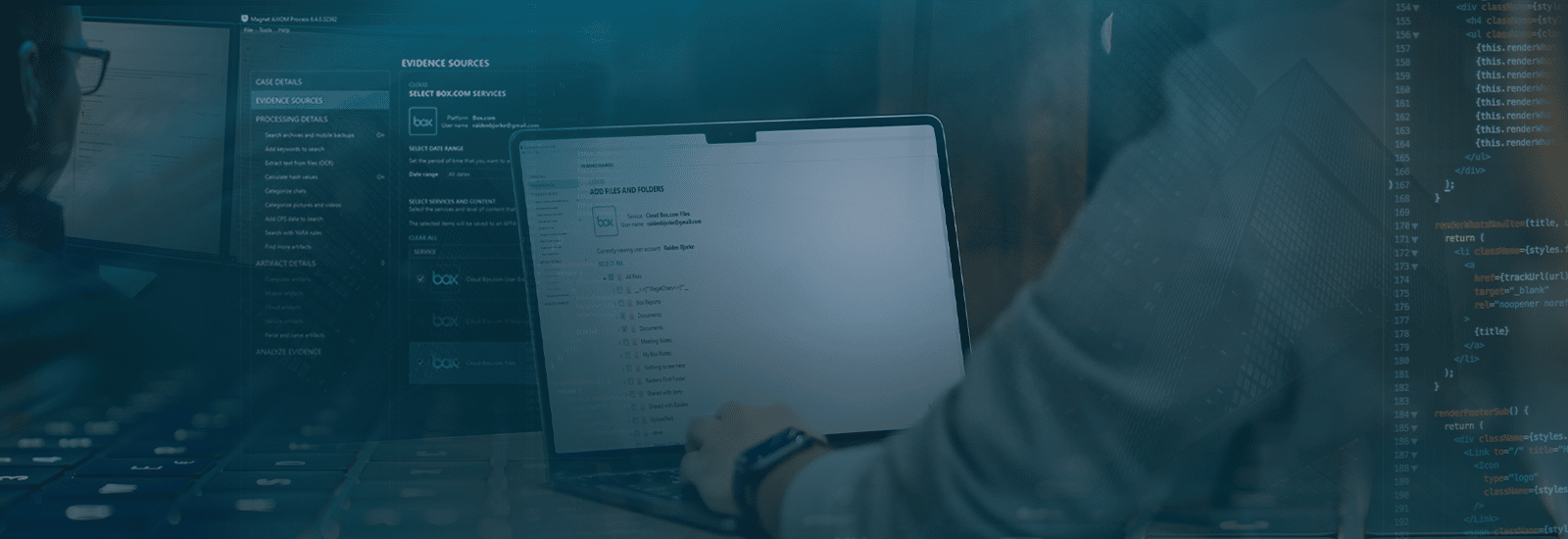
However, with the convenience afforded by cloud tools, companies need to be sure they also have the means to properly investigate and mange their data stored in the cloud. Using AXIOM Cyber you can collect detailed accounts of the files and user activity of your Box.com account, providing visibility into attempts at unauthorized access or theft of your corporate data.
How to Collect From Box.com With Admin Controls Using AXIOM Cyber
Using AXIOM Cyber, you can capture a variety of different artifacts and insights from box.com:
- User Events – information about actions that are triggered by a specific user, including item creation, uploads, and downloads.
- Files – insight into files that stored in the account including file type, name, size and hash, as well as the file owner, collaborators and the access and modification history for the file.
And with Admin Credentials for an enterprise box.com account, you can also capture:
- Enterprise Event – information about administrative events initiated by an admin user related to user credential creation, permission changes, login activity, and syncs.
For a full listing of the artifacts that AXIOM Cyber can collect from Box.com visit the Artifact Reference on our Support Portal.
Once these artifacts have been collected in AXIOM Cyber, there are a range of powerful analytical features like Timeline, Connections and Magnet.AI that can be applied to create actionable intelligence.
Risk of Unauthorized Access to Data on Box.com
Because cloud storage service falls outside of an organization’s network perimeter and can be accessed via the internet, they are prime targets for attackers looking to gain access to a company’s data. The security capabilities built into Box.com have attracted clients that require secure file sharing, including the U.S. Airforce. However even with these measures in place, there is still a need to investigate unauthorized access and data exfiltration is necessary.
According to the IBM Security’s Cost of a Data Breach report, compromised credentials are the most common initial attack vector for data breaches. Credentials can be compromised in a variety of ways but are often the result of poor password management by individual users. This can be the result of employees documenting, sharing and/or reusing passwords, all of which can inadvertently facilitate bad actors gaining access to otherwise secure cloud services.
Another common way for hackers to compromise credentials is to use phishing. According to Verizon’s 2022 Data Breach Investigations Report, phishing activity was present in over one-third of data breaches. Phishing can have a more detrimental impact when the stolen passwords have been reused or recycled as they could then provides access to multiple different accounts and platforms.
Get Magnet AXIOM Cyber Today!
Regardless of what platform your company or clients use to manage data storage and collaborations, with AXIOM Cyber you can quickly investigate suspected unauthorized access and data exfiltration to help protect the businesses valuable data. To try AXIOM Cyber for yourself, request a free trial today!
