Magnet AXIOM Cyber 6.8: Refining Your Evidence Collection and Review
Magnet AXIOM Cyber 6.8 has just been released and delivers great new features and artifacts to keep your investigations moving forward. In this release we have added:
- Remote collection agent placeholders
- Linux memory acquisition
- Pre-processing date filter
- Improvements to the Email Explorer
In addition to these new features, we’ve also updated several artifacts to keep your evidence sources current with the latest apps and services.
You can upgrade to the latest version in AXIOM Cyber or through the Customer Portal.
If you haven’t tried AXIOM Cyber yet, request a free trial here.
Remote Collection Agent Placeholders
New in AXIOM Cyber 6.8: you can now setup placeholders for agents in a remote collection prior to that agent being deployed or checking in. This feature will help streamline building your collection so you can add all of the remote collections at the onset of the investigation and then let AXIOM Cyber progress through the endpoints as they become available.
This feature lets you take a “set it and forget it” approach to your collections, freeing you up to focus on other priorities while AXIOM Cyber takes care of gathering the data, whatever time of night or day the endpoint becomes available—working around the clock so that you don’t have to.
To learn more about this new addition to queued collections, check out this blog and this how-to video from Forensic Consultant, Chris Cone:
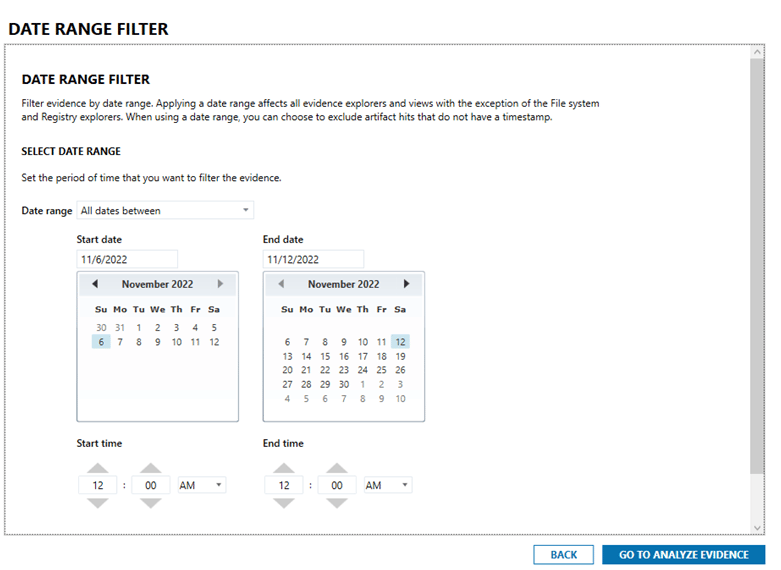
Pre-Processing Date Filter
Another new addition to AXIOM Cyber is pre-processing date filters which gives you the option of setting a date and time range for the artifacts that will be added to a case. Using date restrictions to filter ESI lets you easily limit collected data volumes to applicable timeframes for eDiscovery matters.
Or, if there aren’t specific date restrictions around your investigation, this feature can be used to focus your investigation on the data that is mostly likely relevant based on the when it was generated. This is especially valuable when your investigation involves log file analysis which could results in millions of hits. By pre-processing the data you can reduce the volume of evidence that you need to review, helping you work through your cases quickly and efficiently.
Linux Memory Acquisition
You can now capture the RAM dump of a Linux machine using AXIOM Cyber, providing important insight for malware investigations. Memory data can provide a wealth of information about running applications, network connections, kernel modules, open files, and just about everything else that is wiped out when a computer restarts.
To get the most insight from the data, the collected Linux memory will require some additional carving, but this can be accomplished with a tool like Comae, which is an active (and free) beta program running in Magnet Idea Lab.
Comae is a memory analysis platform that helps diagnose cyberattacks and provides unique data-enrichment and query capabilities. To learn more about Comae and how it can be used with the new Linux memory acquisition, check out the blog post: How to Get Started With Comae.
Improvements to the Email Explorer
You can now expand and collapse the visibility of email attachments to help streamline your review of email evidence. The ability to expand or collapse the attachments in a preview view helps you quickly locate and review messages with attachments to determine if they contain pertinent information for an investigation.
To see Email Explorer in action, check out our recent Tips and Tricks webinar hosted by Steve Gemperle or read more on our Email Explorer blog post.
New and Updated Artifacts
As with all releases of AXIOM Cyber, there is also support for several new and updated artifacts to help keep your investigations current with the latest corporate apps and services developments, including:
New Artifacts
- iOS 16 Recently Deleted Messages
- iOS 16 Reminders
- Safari Suspended State Tabs
- Cloud Google Hangouts Messages (Warrant Return)
Updated Artifacts
- WhatsApp Messages
- iMessage/SMS/MMS
- Private Photo Vault Media
- Snapchat Stories
- TikTok Videos
- Facebook Messenger
- Windows 7, 8, 10 User Accounts
- CUPS Print Jobs
- Chrome Cache Records
Get Magnet AXIOM Cyber 6.8 Today!
If you’re already using AXIOM Cyber, download 6.8 over at the Customer Portal. To try AXIOM Cyber for yourself, request a free trial today!
