Reviewing email evidence with Email Explorer in Magnet Axiom and Axiom Cyber
With computers in our pockets, the number of emails sent and received globally has increased each year since 2017. In 2022, there were an estimated 347.3 billion emails sent and received daily around the world. The prominence of email is also reflected in work environments In a recent summary of workplace communication, 74% of employees reported that they rely on email as their primary method of communication.
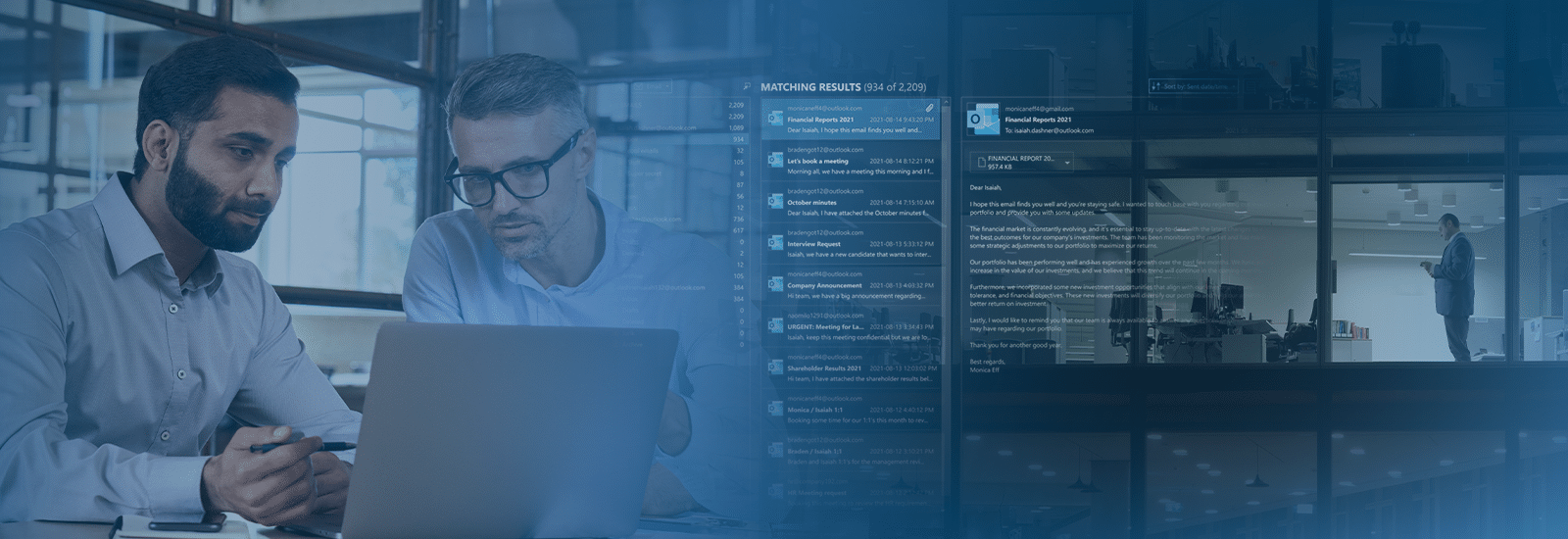
We introduced Email Explorer for Axiom and Axiom cyber to help examiners quickly and efficiently review email data for potential evidence. This interface helps you manage emails by presenting them in an intuitive and familiar format that mirrors the appearance of common email platforms.
A familiar look at email evidence
Email Explorer presents messages similarly to how the sender and recipient would have initially viewed them, providing important context that may otherwise be missed. Much like a native email platform, Email Examiner offers several filters and search capabilities to narrow in on specific message times or themes to help manage the volume of data.
When reviewing evidence, you can use Email Explorer to tag both the email message and attachments as evidence simultaneously—saving you from the tedious and time-consuming task of manually linking and tagging attachments to emails.
Acquiring email from mobile devices
85% of users access email on their smartphone, making it one of the largest evidence sources coming from your mobile investigations. With Full Filesystem extractions from Magnet Graykey and Magnet Verakey, you can ensure you get the most data possible for your investigations.
Supported email sources
To ensure your investigation includes all of the necessary email evidence sources you may encounter, we have included support for the following:
- Outlook
- Cloud Gmail
- Cloud IMAP/POP
- Cloud Outlook
- Cloud Apple Mail
- Cloud MBOX
You can examine evidence from any of the above sources in Email Explorer using the advanced search and filtering capabilities to help you quickly surface the required email evidence for your investigation. We have also added the ability to easily select and export multiple records for downstream stakeholders.
Use cases for Email Explorer
At the rate at which individuals and businesses generate emails, it’ unsurprising that emails remain a leading evidence source in many investigations.
Below are some examples of how Email Explorer can facilitate the review of email evidence in different examinations:
- Criminal Investigations – Email records can provide critical insights and evidence into the motivation and planning of a range of criminal offenses, such as assault, narcotics, child exploitation, and homicides. With Email Explorer you can review the thread of communication to help identify the parties involved, the timeline of events, and also filter for any messages attachments that may be relevant.
- Malware/Ransomware – Verizon has reported that 94% of all malware is delivered by email. Now, you can filter to review messages with attachments that meet specific criteria to help identify messages containing suspected malware.
- Phishing and Business Email Compromise– 96% of companies reported email-related phishing attempts, making it one of the most common email-based threats. With Email Explorer’s search capabilities, you can identify common link attributes or wording to find messages that may be related to phishing attempts. Using the Markup Viewer in Email Explorer, you easily view an email’s header and HTML or XML source code to quickly uncover malicious URLs due to a phishing or business email compromise attack. The Markup Viewer preview card is supported for all email artifacts with an HTML or XML source.
- Legal Review and eDiscovery – The volume of messages associated with legal investigations can be exceptionally high. You can easily review email evidence with Email Explorer’s familiar interface, which provides context to the original message threads. Search and filter criteria also help to narrow down large volumes of potential evidence.
- Insider Trading or Fraud – Email records can be critical in establishing a timeline of events and the parties involved. With Email Explorer, you can sort messages based on the timeline and review them in a format mirroring the original message to provide context and the progression of the communications.
- Data Exfiltration – Emails can be a common exfiltration technique from corporate networks. You can quickly identify messages that include attachments meeting specific criteria or search for references to file-sharing links in the message content with Email Explorer. Date and time filters also facilitate building a timeline of messages about suspected data exfiltration.
- Employee Misconduct – To identify workplace harassment or inappropriate employee conduct through email, Email Explorer‘s global search bar captures hits for terms included in messages. At the same time, time filters can narrow the investigation to specific windows during which incidents are reported to have occurred.
To see Email Explorer for yourself, request a free trial of Axiom or Axiom Cyber today!
