
How EDR, XDR, and SIEMs complement DFIR
Chances are if you have EDR (endpoint detection and response) tools, your cybersecurity posture is mature enough that you also have DFIR (digital forensics and incident response) tooling as well. But you may be wondering: how they overlap (if at all)? Do EDR tools and DFIR tools do the same thing, or do they complement each other?
The short answer is that EDR and DFIR tools complement each other. While EDR tools provide real-time monitoring and basic investigative capabilities, they are limited in their forensic depth. DFIR tools step in to perform the deep dive analysis necessary to ensure that security incidents are fully understood and remediated. Moreover, with the integration of platforms like Magnet Nexus, which can forensically conduct collections across networks and handle multiple collections simultaneously, the forensic soundness and integrity of the data extracted during these investigations are assured, providing a reliable foundation for incident response.
Incident response framework
The most widely adopted framework that outlines the incident response (IR) process is from National Institute of Standards and Technology (NIST) Special Procedure (SP) 800-61.
There are four key steps within this framework: preparation, detection and analysis, containment eradication and recovery, and post-incident activity.
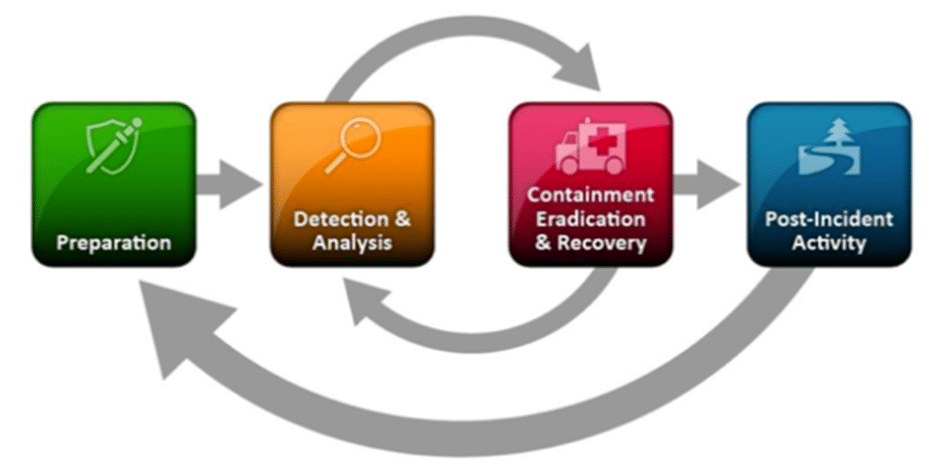
The IR lifecycle provides a foundation for understanding how both EDR tooling and DFIR tooling fit in the various stages.
What is EDR?
The EDR market, a term introduced by Gartner analyst Anton Chuvakin, has solutions that “record and store endpoint-system-level behaviors, use various data analytics techniques to detect suspicious system behavior, provide contextual information, block malicious activity, and provide remediation suggestions to restore affected systems.” EDR solutions must provide four primary capabilities which align nicely with the NIST IR framework:
- Detect security incidents
- Contain the incident at the endpoint
- Investigate security incidents
- Provide remediation guidance
EDR tools touch on each step of the framework, with a core focus on the third step: containment, eradication, and recovery. However, EDR’s capabilities are limited when it comes to the deep investigation of security incidents, often only addressing the tip of the iceberg in terms of what happened and when.
One limitation of EDR is its narrow focus on endpoint telemetry, which doesn’t provide visibility into network activity, cloud environments, or how data from mobile or IoT devices contributes to the incident. This is where DFIR tools come in.
What is DFIR?
DFIR can be categorized as two things: digital forensics and incident response. Digital forensics focuses on recovering, investigating, and analyzing digital data, while incident response is dedicated to detecting and remediating security incidents.
While these definitions may sound similar to EDR, the strength of DFIR lies in the acquisition of data and the subsequent deep dive analysis, sometimes from multiple endpoints or data sources. Think of an iceberg: EDR tools investigate the tip, while DFIR tools delve into the entire structure beneath the surface.
With DFIR tools, such as Magnet Axiom Cyber and Magnet Nexus, investigators can acquire and analyze data at a granular level from endpoints, network appliances, and other sources. This allows for a comprehensive extraction of data from endpoints and analyzing an understanding of how a security incident happened, what data was compromised, and who the perpetrator was. Magnet Nexus further bridges the gap between EDR and DFIR tools by providing visibility across the network, like an EDR tool, but also forensically extracting data from endpoints and analyzing for critical digital forensic artifacts.
Going back to the NIST IR framework, the final step of the process is post-incident activity, which usually focuses on lessons learned that feed into the preparation stage. Without an intimate understanding of how and who is best performed by a digital forensics tool, these stages of the IR process are not properly completed.
Additionally, many businesses—specifically those in highly regulated industries like financial services or healthcare—are under increasing pressure and regulatory requirements to report on known data breaches and provide details within a defined timeframe. For example, GDPR mandates that organizations must report a notifiable breach without undue delay within 72 hours of becoming aware of the breach.
Magnet Axiom Cyber
DFIR tools like Magnet Axiom Cyber are essential for businesses to acquire data from remote endpoints and analyze data from multiple sources like Windows, Mac, or Linux devices in addition to mobile devices, cloud-based apps or storage services such as AWS or Azure, not to mention the ever-expanding number of IoT devices. Axiom Cyber has the ability to conduct a “deep dive” into digital forensic artifacts. By locating these artifacts and presenting them in an artifacts-first approach, gets you to the critical data more quickly and in an easy-to-understand format.
Once analysis is complete, Axiom Cyber has comprehensive reporting functionality that can produce a range of reports: everything from technical exports for review by other DFIR colleagues or a load file for eDiscovery analysts to easy-to-read and understand reports for non-technical stakeholders such as HR or Legal teams.
Magnet Nexus
Magnet Nexus is a centralized digital forensics platform, designed to facilitate the remote collection, processing, and analysis of digital evidence from multiple endpoints. By enabling investigators to connect to and gather data from remote devices—running Windows, Linux and MacOS—across an organization or network, Nexus significantly streamlines the digital forensic process. It allows for real-time acquisition and analysis of data without the need for physical access to the devices, which is particularly useful in distributed environments or during incident response scenarios. Magnet Nexus enhances the ability of forensic teams to perform thorough investigations, ensuring that evidence from remote endpoints is securely collected and analyzed efficiently, aiding in quick and informed decision-making.
The importance of forensic soundness with Axiom Cyber and Magnet Nexus
One critical aspect of DFIR tools is ensuring the forensic soundness of the data. Forensic soundness refers to the integrity and authenticity of the data collected during an investigation, which is crucial for ensuring that the findings are legally defensible and can be trusted in court or regulatory reporting.
Axiom Cyber and Magnet Nexus play a pivotal role in this process by managing remote collections in a manner that preserves the original data’s integrity. Together, they provide a centralized platform that not only facilitates the acquisition of data from various sources but also extracts the data in a forensic manner, to include file hashing. This ensures that the data remains untampered with from the point of collection to the final analysis, making it a trustworthy foundation for any forensic investigation.
A general IR workflow: EDR complementing DFIR
In an enterprise environment, endpoints are monitored by the security operation center (SOC) using an EDR platform alongside other tools such as anti-virus or EPP. These SOC tools generate over one thousand security alerts each day. While technology and automation can alleviate some of the workload, many alerts still require investigation.
SIEM and SOAR tools interact with EDR solutions to help identify when a security event needs to be escalated. When such an event occurs, DFIR tools like Magnet Axiom Cyber and Magnet Nexus are invoked to acquire and analyze data from compromised endpoints. This can include quick triage analysis and deep dive capabilities. Deep-dive analysis uncovers not only the what and when but also the how, who, and sometimes even the why of the incident.
Findings from the DFIR analysis are then shared with SOC teams to ensure comprehensive threat containment and eradication, often using an EDR tool or custom scripting. Without the depth of evidence provided by DFIR tools, organizations are at risk of not fully understanding the root cause of security events, leaving them vulnerable to future incidents.
What about XDR?
XDR (extended detection and response) is an evolution of EDR, addressing some of EDR’s limitations by expanding its visibility beyond managed endpoints to include network, cloud, and other sources. However, even XDR does not replace the deep forensic capabilities of DFIR tools. Magnet Axiom Cyber and Magnet Nexus remain essential for obtaining the complete picture of a security incident.
DFIR solutions for enterprise businesses
Learn more about how Magnet Forensics solutions for enterprise organizations can complement EDR tooling, maintain forensic soundness, and help you respond to security incidents faster and more effectively.
