“Oh no, the suspect ran CCleaner to get rid of the evidence!”
A few questions recently came in about the effects of running Internet history sanitation tools such as CCleaner, when examining a computer looking for internet related artifacts. CCleaner is a product from a company identified as Piriform (www.piriform.com), and a version is freely available online and commonly used to ‘sanitize’ user activity. From the online documentation, CCleaner is said to protect privacy by cleaning out Internet browsing history and temporary internet files.
Running CCleaner on cases when examining digital evidence can have a varying degree of effectiveness, depending on exactly the types of artifacts you are trying to find/recover after its use. CCleaner has the ability to clean and remove information from several different locations, including the registry, the recycle bin and even wipe the disk. For this article, the focus will be on its effectiveness against the ability to recover Internet-related history after CCleaner has been run.
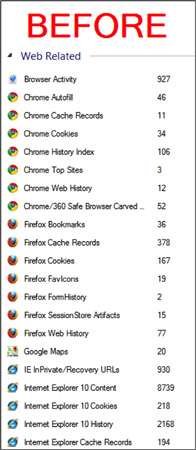
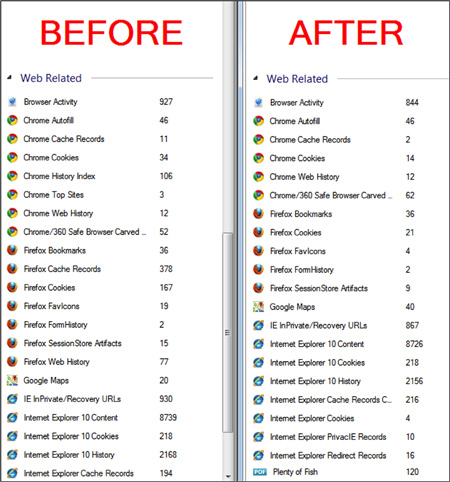
Using a well-used test machine (Windows 7) with several different types of Internet related artifacts, Internet Evidence Finder (IEF) was run using the default options to get a baseline of the artifacts that existed before running CCleaner. The test machine had artifacts from Chrome, Firefox and Internet Explorer 10, as well as numerous other application such as P2P, webmail, etc. Here is a snapshot of the just the web related artifacts found before running CCleaner.
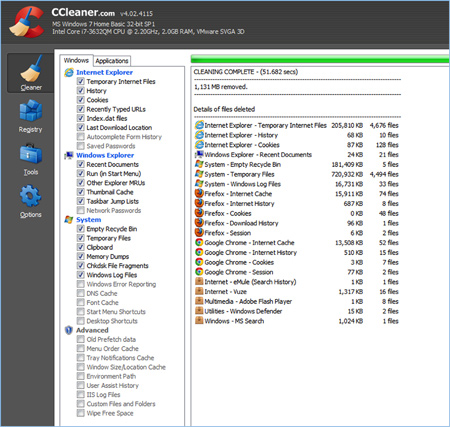
CCleaner was then installed on the test machine, just as a suspect would, accepting the default installation options. From the CCleaner interface, the following options were enabled by default.
CCleaner was then run and received confirmation that it cleaned several locations related to Internet history.
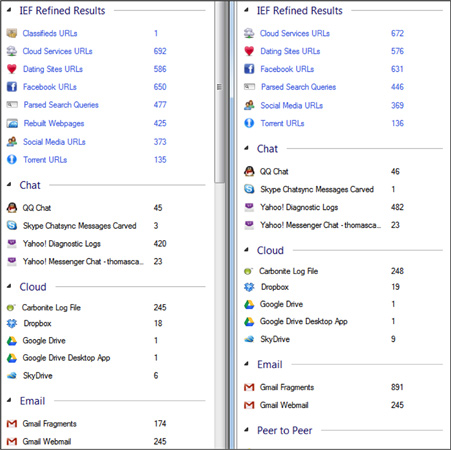
After running CCleaner, the test machine was rebooted and Internet Evidence Finder (IEF) was rerun using the same default options and almost all the artifacts that had been identified before running CCleaner had been found. In fact, some of the artifacts in some categories went up, likely caused by artifacts existing in memory before the reboot and then when the computer was shut down and rebooted, those artifacts were flushed to disk (pagefile).
As many are aware, Internet artifacts are commonly found in memory (which I did not examine in this example), and ultimately end up on disk in the form of the pagefile or hibernation file. Many tools such as CCleaner, have minimal effect on these files and therefore many of the commonly sought after artifacts can still be found.
This should be a clear example and illustration of how important the collection of RAM can be regardless of the type of investigation. It is also a good demonstration showing the importance of searching for Internet-related artifacts even when you may find evidence of ‘sanitation’ tools being used by the suspect. There are several other freely available ‘sanitation’ tools available, each with different varying results. The point of this post is to illustrate that the potential benefits of running a search for Internet related artifacts is well worth the effort, even when you fear they may have been ‘sanitized’.