Magnet AXIOM Cyber 7.1 Is Now Available
We are happy to announce the release of Magnet AXIOM Cyber 7.1. In this release, we have added new features and improvements to help you work as efficiently as possible, including:
- Ability to Search Artifacts by Item ID
- Displaying the Image Hash Verification In Process
- Performance Improvements for Conversation View and Artifact Tagging
We have also included new and updated artifacts to keep your evidence sources current with the latest corporate applications and services. See the full list of artifact updates at the bottom of this post.
You can upgrade to the latest version within AXIOM Cyber or over at the Customer Portal. Or, if you haven’t tried AXIOM Cyber yet, request a free trial here.
If you missed our 7.0 release last month, check out our on-demand webinar where Forensic Consultant, Chris Cone, demonstrates the new features and capabilities of AXIOM Cyber: Webinar: Introducing AXIOM Cyber 7.0
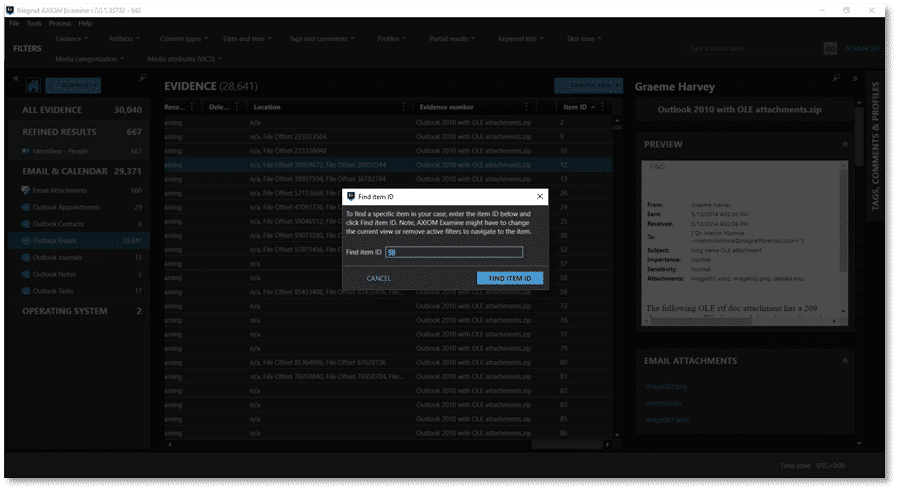
Ability to Search Artifacts by Item ID
There are times in investigations when you need to go back and revisit an artifact. The Item ID gives you a unique reference point to quickly search for specific artifacts so you can gather additional information, without having to comb through data to locate an artifact.
The Item ID is unique to AXIOM/AXIOM Cyber and is included in both Load Files and Portable Case, so downstream reviewers and stakeholders can also easily flag artifacts to request additional context from examiners.
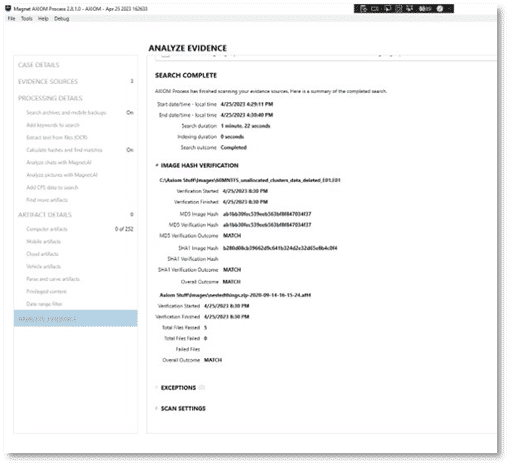
Displaying Image Hash Verification in Process
With different data sources and collection tools used in an investigation, a key step in processing evidence is going to be verifying the image hashes, which provide a digital fingerprint for the files. This verification ensures that during the collections of evidence the image has not been changed or altered which would compromise the integrity of the data.
AXIOM Cyber 7.1 facilitates the process of quickly verifying the integrity of an image with improved visibility of the hash verification. Hash Verification is now presented in the Analyze Evidence window in AXIOM Process with details of common hash formats Secure Hash Algorithm-1 (SHA-1) and Message Digest 5 (MD5) without having to dig into the case logs. Hash verification information also gets written to the Case Information.txt and .xml files.
Performance Improvements for Conversation View and Artifact Tagging
We know how important it is that your tool set keeps up with the pace of your investigations, and so in this release, we have also made some significant performance improvements to AXIOM Cyber to help with your review of evidence:
Conversation View Load Speed
We have vastly improved the speed of loading the conversation view for expanded message threads–making it much faster, even for conversations that include thousands of messages. If you haven’t tried this view recently, give it another try to help you quickly review a series of messages with the added context of the conversation.
Individual Tagging Within Large Datasets
We’ve also greatly increased the speed of tagging items of interest within extremely large datasets to help you work through your review of evidence as efficiently as possible.
New and Updated Artifacts
As with all releases of AXIOM Cyber, there is also support for several new and updated artifacts to help keep your investigations current with the latest corporate apps and service developments, including:
New Artifacts
- iOS Device Wallpapers
- Microsoft Office 365 MRU
- Snapchat Geolocation (Warrant Return)
- Windows Program Compatibility Assistant Records
Updated Artifacts
- Android Installed Applications
- Google Account Information (Warrant Return)
- Google Login History (Warrant Return)
- iOS Device Information
- Linux Operating System Information-icon Operating System Information
- Motion Photos
- TikTok Media
- WhatsApp Messages
Get Magnet AXIOM Cyber 7.1 Today!
If you’re already using AXIOM Cyber, download 7.1 over at the Customer Portal. To try AXIOM Cyber for yourself, request a free trial today!
