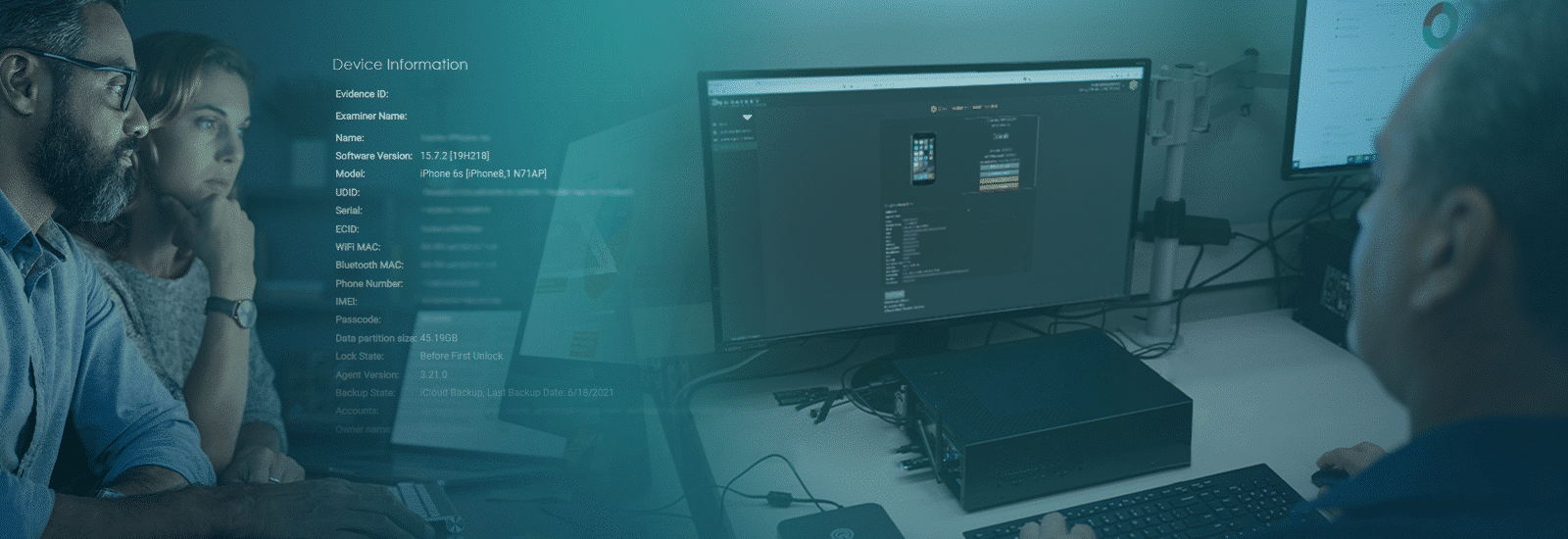
Best Practices For Examining Mobile Consent Devices
Regarding digital evidence, mobile devices are some of the most crucial evidence types you may encounter in your investigations. They contain a wealth of information like communication data, multimedia files, location information, and more. It’s not just the suspect’s phone that can play an essential role in an investigation. Victims, witnesses, and other third parties involved in an investigation may have information that could help. Is examining a “consent device” different than examining a seized device? In this blog, we will answer that question, and more so, the next time you encounter a consent device, you are well equipped to process it.
What is a consent mobile device and why are they important?
A consent mobile device has not been seized by a search warrant or other lawful power of seizure. Simply put, the device’s owner has voluntarily given their permission to law enforcement to examine the device and collect information from it. Typically, in this scenario, the owner will most likely provide the device passcode to facilitate access. In most cases, consent devices are obtained from victims or witnesses rather than suspects, where a device is usually seized from a suspect.
Technical challenges
In some instances, evidence from consent devices can be just as challenging to examine as seized devices, depending on how the owner has set up the device. For example, the device owner tells you they have a photograph on their phone and provides consent to access and collect the photo.
Upon examination, you discover the photograph is in cloud storage. In this instance, the examiner must return the device to the owner, ask them to re-enable network connectivity, download the picture from the cloud save it locally, and then isolate the device again.
In another example, the photo is embedded in a third-party application. If you only have consent to access the camera roll, you need further consent to access the third-party application.
Having first-hand experience in handling these types of technical challenges can make or break an investigation. One thing to remember is that device owners are usually not involved in investigations, nor do they have much knowledge of digital forensics. An investigator handling the examination of a consent device generally must be quick on their feet, and be well versed in all things technical, in order to know how to approach a device examination in a timely and legal manner with the best forensic tools available.
Time constraint issues
There are occasionally complexities with examining a device – consent can be withdrawn at any stage during the investigation by the device owner. If they change their mind, at any point, they can request their device back. Depending upon your jurisdiction’s applicable relevant policies, you may be required to immediately stop the technical examination, which means you might not get a complete extraction.
Also, once consent devices are processed, they are returned to their owner. This means that the actual evidence is still on the device while you only have a forensic copy. In this situation you can request that the owner maintain the device pending the investigation’s completion to preserve data. This creates a heightened complexity associated with assuring the device is available for further review.
Always ensure that you treat the device with care and follow best practices for preserving digital evidence, whether the device is collected via consent or seizure. But, as always, follow the direction of the appropriate legal authority in your jurisdiction.
Note: The material and information in this resource are based on 30+ years of in-the-field experience from the Magnet Digital Forensic team and is intended for general information purposes only. As always, please refer to your department’s policies and procedures and state, local, and federal laws relating to digital forensics and investigations.
