Acquiring Memory with Magnet RAM Capture
Recently, we released a new free tool that allows investigators to acquire the memory of a live PC. Customers using our IEF Triage module will already be familiar with this tool, as it’s used to acquire evidence from live systems. In realizing that others could benefit from our RAM capture tool, we decided to release it free to the forensics community.
Memory analysis can reveal a lot of important information about a system and its users. There are often instances where evidence stored in memory is never written to the hard drive, and may only be found in the pagefile.sys or hiberfil.sys. Memory analysis is essential to many malware and intrusion incidents and can be imperative in recovering valuable evidence for almost any PC investigation. Running processes and programs, active network connections, registry hives, passwords, keys and decrypted files are just a few examples of the evidence that can be found in memory. Many web apps, like Gmail, or private/incognito browsing modes will only store data in memory meaning the evidence cannot be recovered from the hard disk.
Magnet RAM Capture supports both 32 and 64 bit Windows systems including XP, Vista, 7, 8, 10, 2003, 2008, and 2012. It will acquire the full physical memory quickly and leave a small footprint on the live system being analyzed. For my system it took about 3 minutes to image an 8 GB RAM dump.
How to Run Magnet RAM Capture
Running Magnet RAM Capture is very straightforward. The standalone executable can be run from either a USB stick or from the local machine.
Users will need to specify two items prior to starting acquisition: (1) where to save the captured data, and (2) whether the files should or should not be fragmented. Fragmentation is turned off by default, however, if you are running the utility from a FAT32 formatted USB stick and the host RAM you are capturing is greater than 4 GB, then we recommend fragmenting your files to adhere to the FAT32 maximum file size limitation. Magnet RAM Capture creates a raw data dump with a .DMP extension. If you are saving the image back to the USB, you’ll want to ensure that there is enough space for the acquired memory.
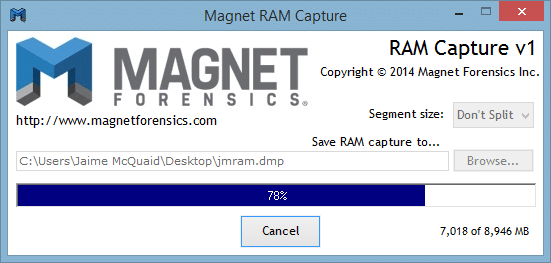
Once the location and segment size has been selected, you can hit start and the utility will begin capturing the system’s memory. A progress bar will provide the investigator with the status of the collection. Once the collection is complete, the captured memory can be analyzed with your favorite memory analysis tool.
Analyzing Memory Collected with Magnet RAM Capture
Since the memory collected by the utility is stored in a raw data format, it can be analyzed by most memory analysis and forensic tools including IEF, Volatility, and Mandiant Redline.
To analyze the memory dump with IEF, select Images from the main IEF screen and upload the raw .DMP file acquired with Magnet RAM Capture.
IEF will load the RAM dump and perform a sector level search (by default) since there is no file system associated with the unstructured raw data.
Once loaded, you may select which artifacts you wish to include in your search (searching for everything will yield the most complete results) and begin your search just like any other image file being loaded. Upon completion of the IEF search, Report Viewer will display any artifacts found within your memory dump. Because Images was selected when the RAM dump was loaded, IEF will report any evidence it finds as a physical sector. If you want to see the results as a file offset, choose Files & Folders when loading the .DMP file and it will adjust to which ever value you prefer.
Physical memory stores a wealth of information, and capturing memory from a live system should be a part of any investigator’s workflow. Whether you’re working a malware infection, intrusion incident, or IP theft, there is bound to be evidence found in memory that could be vital to your investigation. Magnet RAM Capture is a fast, free tool that can be added to your toolkit and it works great with your favorite memory analysis tools.
Please let me know if you have any questions, suggestions or requests. I can be reached by email at jamie.mcquaid@magnetforensics.com.
Here are some related resources you might also be interested in:
- Download Magnet RAM Capture: Download Now
- More Information about IEF
- Attend an IEF Demo: Register Now
Jamie McQuaid
Forensics Consultant, Magnet Forensics
