Magnet AXIOM Cyber 7.7: Try the New Integration with REVIEW SaaS Free Trial
We’re excited to announce that the latest version of Magnet AXIOM Cyber is now available!
In this release, we made several enhancements to streamline your workflow and uncover insights faster, including:
- New Integration with Magnet REVIEW SaaS Free Trial
- Improved Magnet.AI Results for Short Videos
- New Memory Artifact added to Comae Integration for Malware Investigations
- Signed Windows Agent for Reliable Remote Collections
We’ve also updated and added to our artifact support (updates are at the end of this blog.)
Check out the release notes here for a complete summary of all updates made in this release.
Upgrade to AXIOM Cyber 7.7 within the AXIOM Cyber interface or through the Customer Portal. Haven’t tried AXIOM Cyber yet? Request your free trial here.
Free Trial: Share and Collaborate on Evidence Review with Magnet REVIEW
As part of AXIOM Cyber 7.7, we’re excited to announce an early access free trial of an upcoming new SaaS-based version of Magnet REVIEW for existing AXIOM and AXIOM Cyber customers!
Enabling timely and effective sharing of digital evidence is vital to keeping your investigations moving. Magnet REVIEW helps you easily and securely share digital evidence from all your sources with your investigative teams and stakeholders so you can work together to finish cases faster.
REVIEW is integrated with AXIOM Cyber, so you can securely share your cases directly from the Examine export dialogue, and your stakeholders can access REVIEW from any web browser with no special hardware or software required.
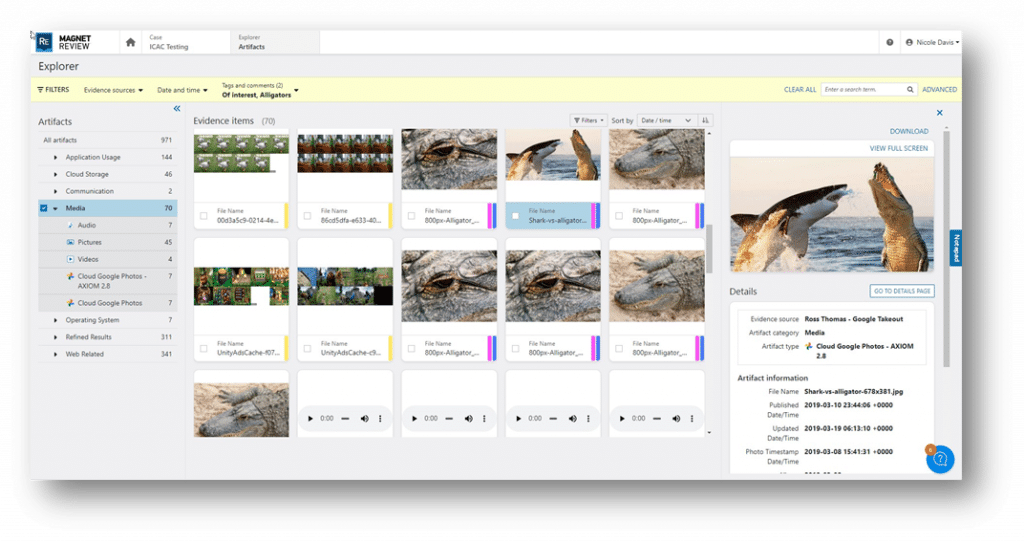
With this new Magnet-managed SaaS option, you can deploy REVIEW easily and securely throughout your organization without installing and managing the system yourself. Create an account via your browser, and you can immediately start sharing cases with your investigators and other stakeholders.
Our early access free trial is open to existing AXIOM Cyber customers and will allow you to experience REVIEW for free before our official launch. You can securely share cases from the AXIOM Cyber Examine export dialogue, review evidence using REVIEW’s intuitive user interface and powerful search tools, collaborate using tags and comments, and generate and share detailed reports.
AXIOM Cyber customers can create a free trial account by visiting the Magnet REVIEW site or from within Examine by clicking on the upload flow from the dashboard.
For more details on the REVIEW SaaS early access free trial, check out our new blog.
Upcoming Webinar December 13th: What’s New in Magnet REVIEW 5.3
Our latest version of REVIEW makes it even easier for you to bring your stakeholders and their evidence together, with a revamped user interface to help them quickly find the evidence that matters and a new delivery option designed to simplify deployment and management.
Join Magnet Forensics’ Nicole Davis and Jonathan Evans for a walkthrough of the powerful new experiences in REVIEW 5.3, including cross-evidence views, updated evidence previews, and more!
Register for the webinar here.
Improved Magnet.AI Results for Short Videos
We made exciting improvements to the analysis capabilities of Magnet.AI on short videos! These enhancements significantly improve the accuracy of the media classifiers for short videos under 2 minutes in length. After internal testing, we saw an improvement of ~70% in media classifiers identified over AXIOM Cyber 7.6.
Magnet.AI helps you to cut through the noise, surfacing relevant videos quickly for further analysis. You can analyze videos for matches on specific items such as documents (cards and IDs), handwriting, human faces, hands, money, screen captures, and documents (paper), among several more.
Due to the wide range of item classifications available, you can use Magnet.AI for several investigations such as HR investigations ( harassment, bullying, and policy violations), fraud, data exfiltration, and IP theft.
New Memory Artifact added to Comae Integration for Malware Investigations
This new memory artifact added to the Comae integration in AXIOM Cyber, Windows Executive Object Callbacks, gives examiners another checkpoint on the system to understand whether anything malicious, such as malware, was installed.
Windows Executive Object Callbacks are a list of functions called when the operating system actions various tasks like opening files, creating processes, creating threads, accessing the registry, and more. When malware executes on a system, it will add its own function to this list. If you find the function in code that is non-Microsoft signed code, then it can be considered highly suspicious. Malware that typically uses this technique is likely to be a rootkit.
To learn more about the integration of Comae for memory analysis, read our blog “Comae Memory Analysis Capabilities Integrated Into Magnet AXIOM Cyber.”
Signed Windows Agent for Reliable Remote Collections
One of the methods by which modern antivirus solutions detect malicious agents or files is by checking for a signed certificate with a digital signature from a trusted entity. The file may be deemed potentially malicious if a signed certificate is missing. An alert will then be triggered, or the file will be quarantined until an analyst can verify whether it’s a threat or a false positive. To ensure you can easily and reliably collect from Windows endpoints, AXIOM Cyber’s remote acquire agent is now signed to avoid potential false positives and subsequent disruptions to your investigation.
New and Updated Artifacts
This release includes several new iOS artifacts and updates to existing iOS, Android, Windows, and macOS artifacts to help keep your mobile and computer investigations current with the latest apps and services:
New Artifacts
- DJI Media (iOS and Android)
- Network Interfaces (iOS)
- Private MAC Addresses (iOS)
- Executive Object Callbacks (Memory) (available in AXIOM Cyber Only)
Updated Artifacts
- Device Information (iOS)
- Edge Chromium Autofill (Windows)
- Facebook Messenger Messages (iOS and Android)
- Find My Items (macOS)
- Google Chats (Takeout and Warrant Return)
- ICQ 10 Messages (Windows)
- Instagram Direct Messages (iOS and Android)
- Message Preferences (iOS)
- Signal (Android)
- Snapchat Messages (Warrant Return)
- Slack (Cloud Acquisition, Data Export)
- Various Biome artifacts for iOS 17 (iOS)
- WeChat (Android)
Get Magnet AXIOM Cyber 7.7 Today!
Download AXIOM Cyber 7.7 over at the Customer Portal or upgrade within the application. Haven’t tried AXIOM Cyber yet? Request your free trial here.
