
Recover iOS App Screen Layouts with the New iOS Home Screen Items Artifact
As investigators, part of our job includes providing an accurate account on the evidence recovered from the incident under investigation. Including details down to the look and feel of how a device is setup and how a user interacted with it goes a long way in providing the context needed for our casework.
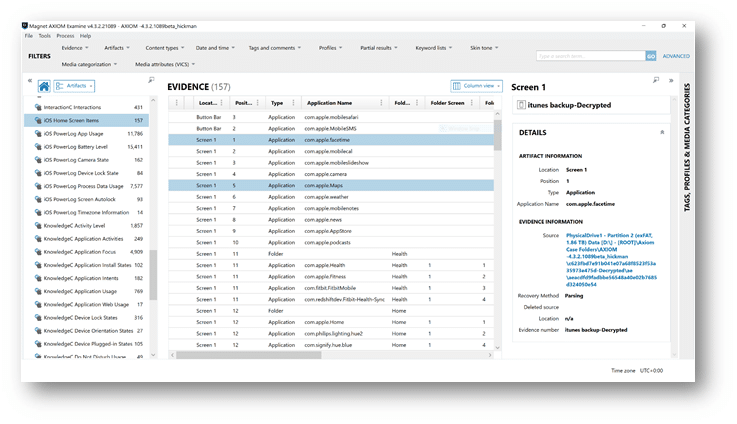
In the latest release of AXIOM, examiners now can quickly identify and report on how a user had their applications arranged with the new iOS Home Screen Items Artifact.
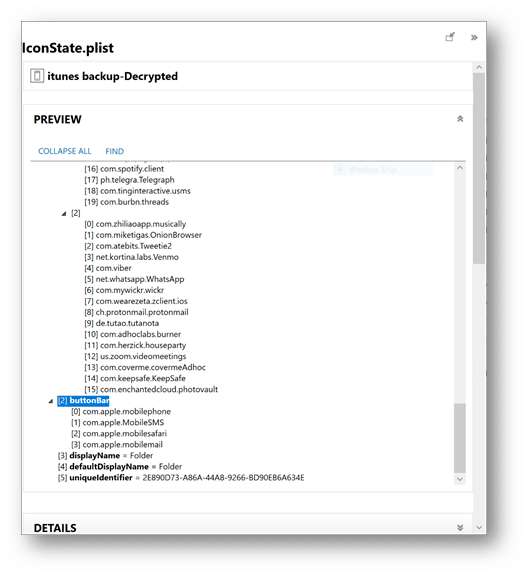
AXIOM will parse the iconstate.plist—which can be found in iTunes backups, logical, or file system acquisitions—to provide the location of where and how icons are located on an iOS device.
Examiners can find the plist manually here: private/var/mobile/Library/SpringBoard/ or by simply clicking on the source link under the details panel from within the iOS Screen Items Artifact.
The iconstate.plist also contains a key for the buttonBar, which provides information regarding what Apps are found on the device’s button bar.
You can find the iOS Home Screen Items Artifact nested under the Operating System Artifacts. AXIOM will provide the examiner with the application name, location (button bar, screen 1, etc.), position, and whether or not it’s located in a folder.
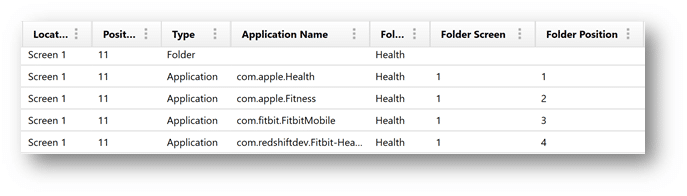
As you can see in the image below, AXIOM will also list the folder with the applications nested inside and their position as well.
If you have any questions on this artifact, or have ideas for new artifacts you’d like to see added to AXIOM, please don’t hesitate to reach out to me at trey.amick@magnetforensics.com.
