
The top 10 updates to Magnet Axiom Cyber in 2023
We bring great updates to Magnet Axiom Cyber every month and sometimes with so many fantastic new features it can be easy to lose track. We thought we’d take this opportunity to summarize a few of the most noteworthy features that we introduced to Axiom Cyber over the past 12 months, including memory analysis, Magnet Verakey connection, and so much more! Check out our top 10 updates to Axiom Cyber in 2023.
1. New memory analysis capabilities with Comae
This year, we introduced new memory analysis capabilities to Axiom Cyber! Now, you can analyze Microsoft crash dumps in Axiom Cyber with the integration of Comae memory analysis technology. Comae adds improved support for current Windows operating systems, new insights for modern threats as well as greatly improving the speed of processing memory in Axiom Cyber.
To see how to use Comae Memory Analysis in Axiom Cyber, check out our blog: Comae Memory Analysis Capabilities Integrated into Axiom Cyber.
2. Email relationship linking in load files
It’s estimated that 347.3B emails are sent a day (in 2023), so it’s not surprising that email is a key source of ESI in eDiscovery collections. We added relationship linking for email messages and attachments in load files this year. When selecting emails or attachments for export you now have the option to include the parent and any sibling attachments associated with the communication.
To read more about this development check out our blog: Supporting eDiscovery with Email Relationship Linking in Axiom Cyber Load Files.
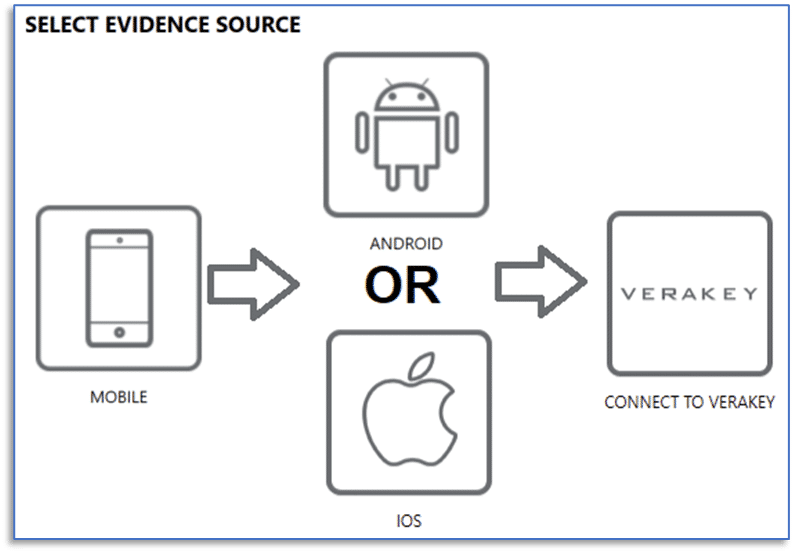
3. Connect to Magnet Verakey
When your tools work together, you can stop fighting the workflow and focus on your investigations. The integration of Axiom Cyber with Verakey streamlines your end-to-end workflow, from acquisition to analysis and reporting. Acquire and process mobile images directly from Verakey, an advanced mobile forensic solution for consent-based, full file system data extractions from iOS and Android devices.
To learn more about how you can use Verakey with Axiom Cyber check out our latest blog: How to connect Magnet Axiom Cyber directly to Verakey for mobile device investigations.
4. Privileged materials
In many eDiscovery cases, there will be set parameters around what evidence can be included in the scope of the investigations. Easily load keywords related to privileged evidence and Axiom Cyber will automatically tag the artifacts or exclude them from the Artifact Explorer. This feature helps to expedite the review of privileged materials and helps ensure a more accurate and efficient process. Learn more about tagging privileged materials here.
5. Shared agents
Teams of examiners celebrated this year as they were able to simplify and save time accessing data from endpoints that were previously deployed to using Shared Agents! Now, any of your Axiom Cyber instances can call out to an existing Axiom Cyber agent without having to deploy a new, unique ad-hoc agent.
To learn more about how Shared Agents can be used for your team, check out this blog.
6. Export cases directly to Magnet Review SaaS
Big news this year: we launched an early access free trial of an upcoming new SaaS-based version of Magnet Review for existing Axiom and Axiom Cyber customers! Magnet Review helps you easily and securely share digital evidence from all your sources with your investigative teams and stakeholders so you can work together to finish cases faster.
Review is integrated with Axiom Cyber, so you can securely share your cases directly from the Examine export dialogue, and your stakeholders can access Review from any web browser with no special hardware or software required. Learn more about Review SaaS early access free trial here.
7. Millisecond precise timestamps for more accurate analysis
In any investigation, digital forensic examiners must address key questions, including the pivotal “when” and “how.” Precise timestamps play a vital role in answering these questions, whether by constructing timelines, correlating events, or connecting relationships between various actions and users.
But when some events occur at machine speed, a lot can happen in just one second!
Now, millisecond precise timestamps are supported throughout Magnet Axiom and Magnet Axiom Cyber and all artifacts where millisecond data is available, such as in Timeline, Connections, and log entries. Ultimately this enables you to quickly analyze chronologically sorted artifacts with improved accuracy.
To learn more about this enhancement, check out the blog post “Improve investigation accuracy with higher timestamp resolution.”
8. Signed Mac and Windows agents, and a new partnership with Jamf
The use of Mac computers for business applications continues to grow steadily. In U.S.-based enterprise companies (1,000+ employees), IDC reported the usage of macOS devices is around 23%, up 6% from 2 years prior. But Apple’s update to their security controls prevented data collection from a Mac endpoint without triggering a Transparency Consent and Control (TCC) prompt on the endpoint—which limits acquisition abilities for investigations requiring a more subtle approach. To ensure you can easily and reliably collect from remote Mac endpoints, we have updated Axiom Cyber’s Mac agent and had the new agent signed by Apple.
To facilitate deploying the new signed Mac agent to devices running macOS, we have also partnered with Jamf, the industry standard in managing and securing Apple endpoints. When we spoke to customers investigating Mac endpoints, Jamf emerged as the primary deployment tool for Mac and the industry standard in managing Apple endpoints.
Don’t miss our co-presented webinar on January 10th with Alec Quinn, Systems Engineer – Developer Relations at Jamf and Dean Carlson, Senior Product Manager at Magnet Forensics. Hear more about these challenges and how Axiom Cyber and Jamf Pro help you more reliably and seamlessly collect data from macOS endpoints.
9. Microsoft 365 and Teams client credentials authentication
Cloud investigations continue to play a pivotal role in corporate investigations as more critical data moves to the cloud. Approximately 60% of corporate data is stored in the cloud which represents a 2x increase from 2015. Accessing that data can be challenge – but with new enhancements to our Microsoft 365 and Teams collection workflow you can now authenticate and access data with client credentials. If your organization’s data access control policy prohibits the use of global admin accounts and/or an account’s username and password to authenticate and access data, upgrade now and use client credentials instead to meet your organization’s security, privacy, and compliance policies while collecting the comprehensive cloud data you need for your investigations.
Client credentials are configured in Azure and can be set up with read-only access with the option to choose what data can be accessed. You can also set client credentials to expire if governance rules require time-limited access to data. Learn how to set up client credentials in Azure in our knowledge base article “Sign in to Microsoft using Client Credentials” (Support Portal login required.)
10. Remote endpoint file listing
A complete file listing can help you answer key questions such as “was this file still present on the endpoint after an attack?” or it can help you estimate and answer stakeholders who want to know “How long will it take to collect and process this case?”
Quickly generate a complete index of the files and folders currently on a remote endpoint and preserve that index and search it for use during an active investigation or for future reference. To learn more about this new feature and three ways you can use it in your next investigation, check out the blog post: “three ways to use remote endpoint file lists to streamline your investigations.”
Want to try these features for yourself? Learn more about how Axiom Cyber can simplify your investigations and get a free trial here.
