Mobile anti forensics and the impact on evidence recovery
Magnet Forensics is proud to feature the great work of our academic colleagues’ research as a resource for the digital forensic community. This inaugural piece is courtesy of Jacob Heasley, M.S. and derived from his research and approved thesis at Purdue University, “Anti Forensics for Mobile Devices: Exploring Apps Encountered by Digital Forensic Investigators” doi: 10.25394/PGS.29647397.
If you are a student or academic researcher interested in partnering or sharing your academic research for further reach, please let us know.
Authored by Jacob Heasley, Purdue University
This research explores a selection of anti forensic mobile apps on Android and iOS using Magnet Axiom: Snapchat’s My Eyes Only, Samsung Secure Folder, SpoofCard, and Wasted (an Android panic-wipe app). Each application was installed on controlled test devices on both Android and iOS, populated with realistic data (photos, videos, calls, and messages), imaged, deleted, and imaged again. Analysis focused on the recoverability of stored artifacts, the effectiveness of built-in security or wipe mechanisms, and the potential countermeasures available to investigators.
Application behavior and key findings
- Snapchat’s My Eyes Only
The My Eyes Only (MEO) feature allows users to store private media protected by a four-digit PIN.
- Artifacts located: Within the Android file system, investigators located memories.db and memories_meo_confidential databases under /data/data/com.snapchat.android/databases/.
These contained entries for both public and private media, and a hashed version of the MEO PIN.
Table 1. Memories entry table from Android Snapchat image
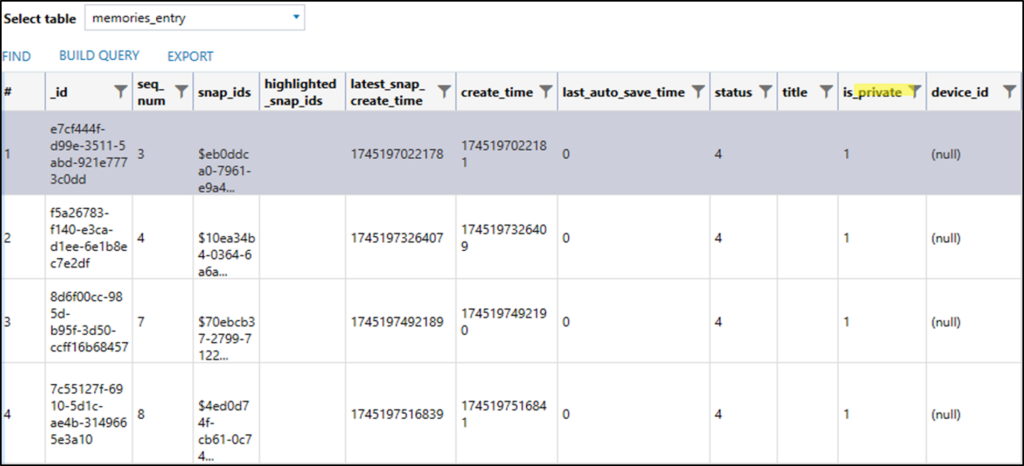
Note. This figure shows the Snapchat memories table. The is_private column indicates if the media has been added to MEO or not.
Table 2. Snapchat MEO hashed_passcode table from Android Snapchat image
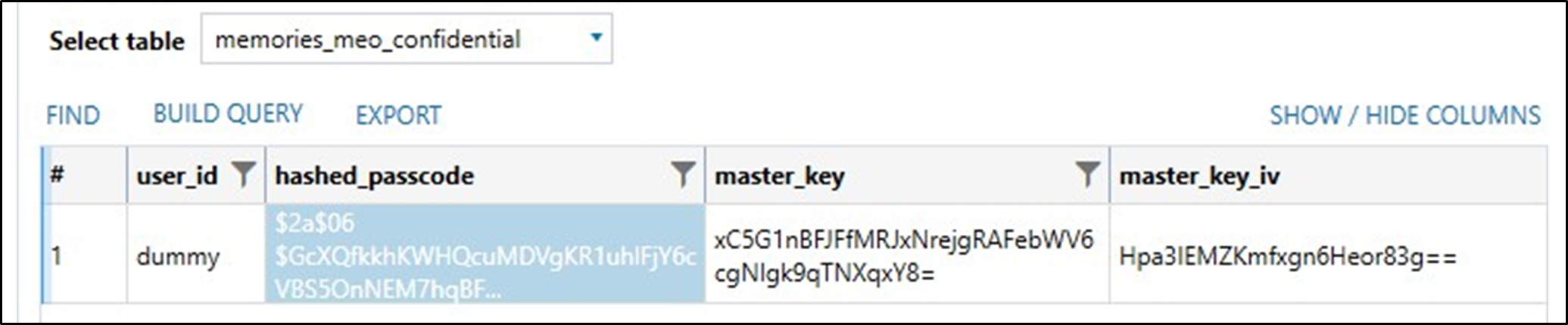
- Forensic results: The hashed PIN (bcrypt format) was successfully brute-forced using the open source password cracking software, Hashcat, revealing the original 4-digit passcode in seconds. Encrypted media files were then decrypted and accessed.
- After app deletion: Minimal traces remained. Once Snapchat was uninstalled, the encrypted data and associated keys were fully removed.
- Implication: MEO offers privacy but relies on weak user PINs that are vulnerable to brute-force attacks once the hash is obtained.
- Samsung Secure Folder – Encrypted containerization
Samsung Secure Folder isolates user data in an encrypted Knox-protected directory.
- Artifacts located: While active, the Secure Folder created separate user directories (e.g., /data/user/10/) containing distinct configuration files (user.xml) and cached media.
Table 3. Samsung Secure Folder user XML file
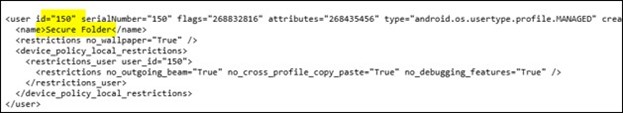
- Forensic results: Files stored within the Secure Folder were recoverable during active use and could be decrypted through device-level extraction with authorized access.
- After deletion: Once the Secure Folder user was removed, its encrypted directory was securely purged. Subsequent imaging revealed only metadata references indicating its prior existence.
- Implication: Secure Folder effectively enforces data hiding and compartmentalization. Once deleted, recovery is virtually impossible without a prior full-disk image or encryption keys.
- SpoofCard – Caller ID masking and secure messaging
SpoofCard provides temporary phone numbers for anonymous calls and messages, a feature often misused in impersonation and fraud.
- Artifacts located: On Android, databases such as call_history, recorded_calls, and spoof_text were found under /data/data/com.spoofcard/databases/. iOS stored traces in native call and SMS databases (CallHistory.storedata, sms.db).
- Forensic results: Even after app deletion, residual logs and cached media persisted briefly in system-level directories. Recorded audio files and message metadata were recoverable on Android, while iOS artifacts required deeper analysis but still revealed contact history and timestamps.
Table 4. Cached recorded audio messages from SpoofCard on iOS

- Implication: Although SpoofCard conceals a caller’s identity in real-time, investigators can still recover metadata and audio remnants from device storage, particularly on Android systems.
- Wasted – Android panic wipe application
Wasted is a security-focused app that automatically locks or erases a device under configurable triggers, such as USB connection detection or repeated login failures.
- Behavior observed: When triggered during forensic acquisition, the app initiated an immediate factory reset, overwriting stored data.
Countermeasures tested:
- Safe Mode: Sometimes prevented the service from loading, allowing limited extraction.
- Wireless ADB Debugging: Enabled data connection before the wipe trigger activated, but with limited extraction capability.
Results: Once the wipe was triggered, data recovery was nearly impossible.
Implication: Wiping utilities like Wasted represent one of the most effective anti forensic threats. Investigators must prioritize isolating the device and securing a physical image before connection events occur.
Broader observations
| App | Platform | Anti Forensic Technique | Data Recoverable | Notes |
|---|---|---|---|---|
| Snapchat MEO | Android/iOS | Data Hiding, Encryption | Partial (if PIN hash obtained) | PIN vulnerable to brute-force |
| Samsung Secure Folder | Android | Data Hiding, Encrypted User Space | Recoverable until deleted | Full purge after folder removal |
| SpoofCard | Android/iOS | Trail Obfuscation | Partial (logs, audio, text) | Leaves residual metadata |
| Wasted | Android | Data Destruction | Minimal | Wipe triggers nearly irreversible |
Implications for forensic practice
This study demonstrates that anti forensic applications vary widely in their effectiveness. While encrypted vaults can often be analyzed through passcode cracking or artifact recovery, wiping tools and isolated secure containers leave little trace once executed.
Forensic professionals should:
- Document app presence early: Determine whether anti forensic behavior may activate.
- Acquire live images: When possible, especially before power cycles or deletions.
- Leverage artifact-level analysis: Even encrypted or deleted apps can leave timestamp, directory, or configuration remnants.
- Stay updated: Rapid changes to mobile OSs continually affect artifact storage locations and recovery success rates.
Anti forensic apps are not niche tools; they are widely available and increasingly sophisticated. Whether through encryption, spoofing, or automated wiping, these apps are reshaping how investigators must approach mobile evidence. The results of this analysis show both the resilience and fragility of digital traces—strong enough to challenge forensic tools yet still revealing valuable metadata when approached methodically.
