Explore Our Digital Investigation Solutions
Magnet Forensics provides modern solutions for enterprise, public safety, and service providers to investigate digital crimes and cyberattacks.
Digital forensics & incident response
The tools you need to access, acquire, analyze, and report on digital evidence and cases.
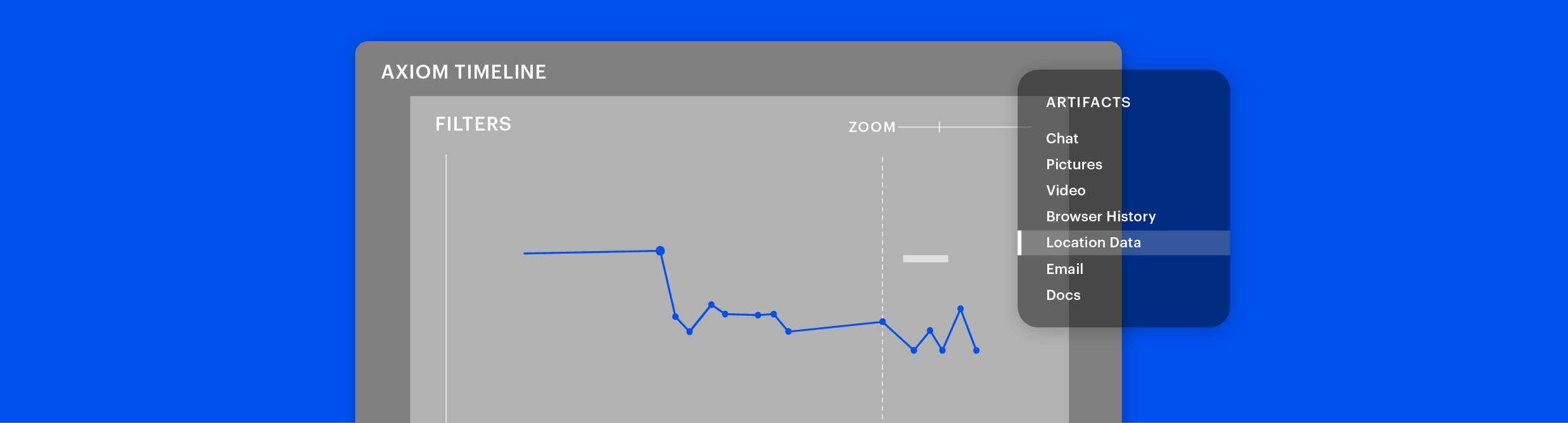
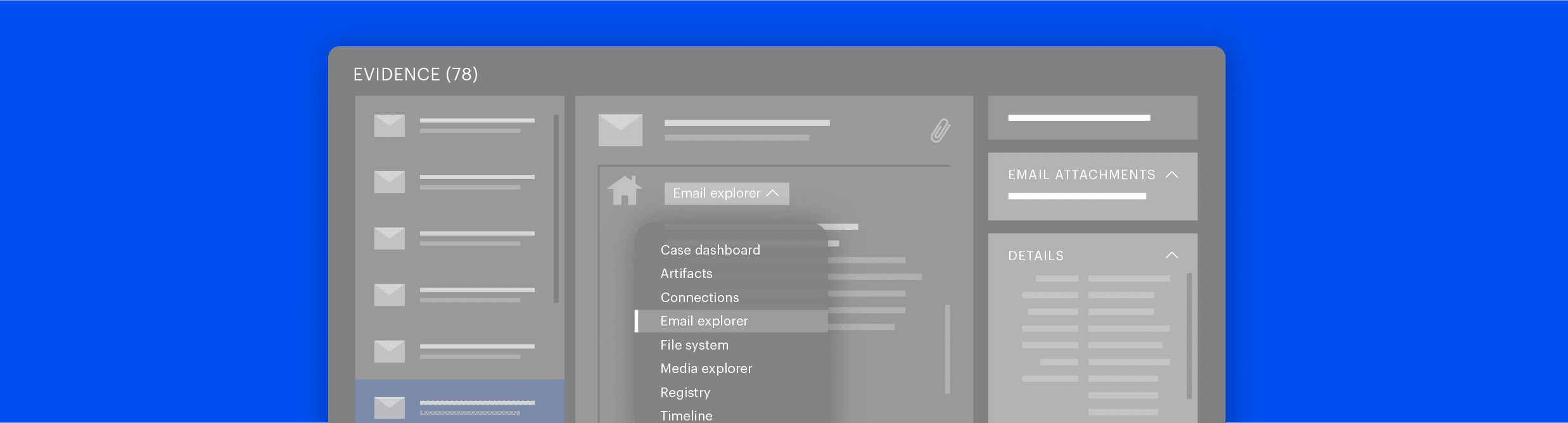
Examine and process digital evidence from mobile, cloud, computer, and vehicle sources all in one case file. Use powerful and intuitive analytical tools to automatically surface case-relevant artifacts and evidence quickly.
A robust digital forensics and incident response solution for businesses and organizations that need to remotely acquire & analyze evidence from computers, cloud, IoT, and mobile devices when faced with cyberthreats.
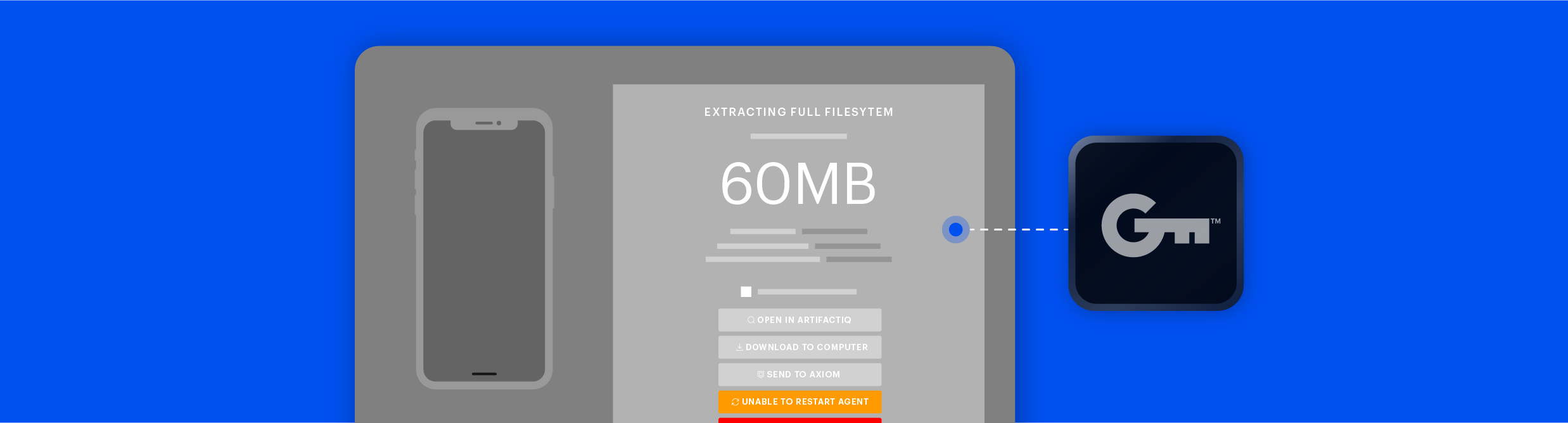
Lawfully access and extract encrypted or inaccessible data from the latest mobile devices & operating systems. Graykey accesses more data than any other extraction technology to help you solve cases faster.
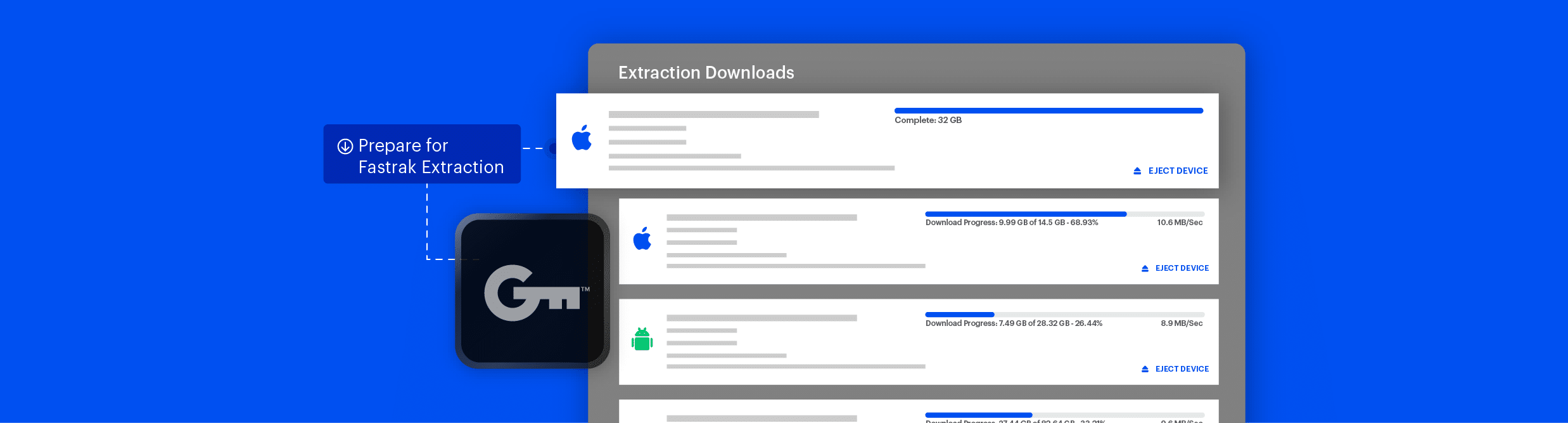
Unleash the power of your Graykey at scale by extracting data from multiple mobile devices simultaneously.
Collect the most comprehensive data extraction, including encrypted and inaccessible data, from iOS and leading Android devices.

Magnet Witness is the evolution of DVR Examiner that now gives you the ability to acquire, review, and analyze video evidence all with one advanced product.
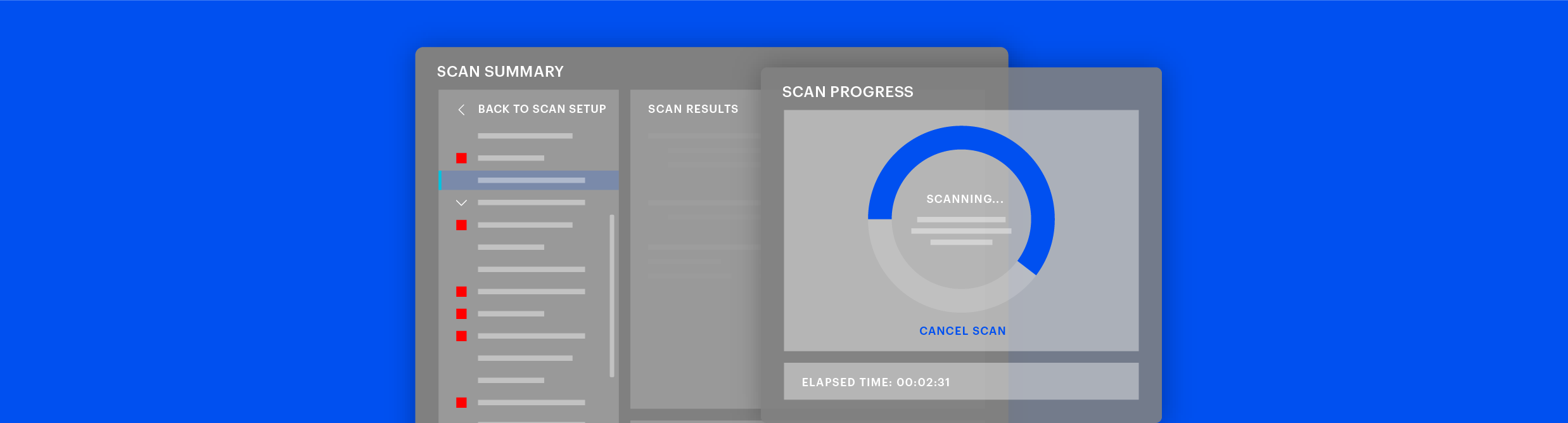
Perform and manage enterprise-wide, large-scale investigations of multiple remote endpoints with speed, scalability, and ease.
Efficiently process and analyze vast amounts of images and videos, automating tasks and uncovering crucial evidence.
Scale up your capacity in digital media investigations by leveraging the collective knowledge, skills, and efforts of your entire team.
Centralize all media material ever collected by your organization, helping you build on each other’s case work and optimize results.
Confidently authenticate images and video, and counter manipulated media.

Streamline your video acquisition and analysis.
Digital evidence collaboration & management solutions
Transform your digital investigations with powerful analytics and collaborate agency-wide, securely and at scale.
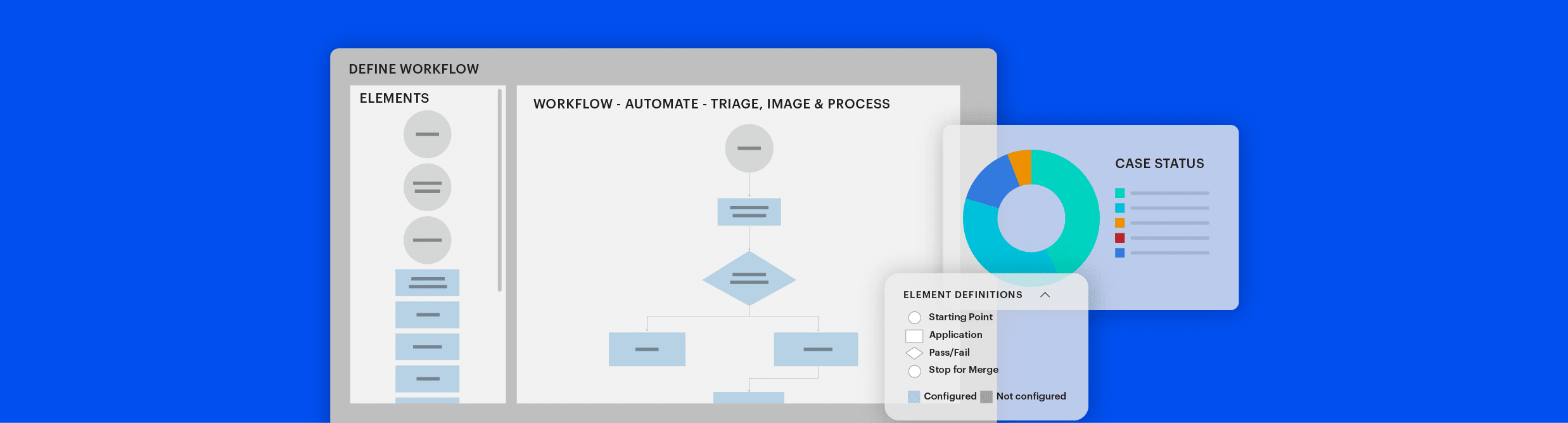
Harness the power of automation to unlock lab capacity, empower your experts, and finish digital investigations faster. Automate processes and tools with streamlined workflows to reduce manual tasks and save time.
Easily & securely share digital evidence with investigative teams, including non-technical reviewers and other stakeholders. Investigators and other stakeholders can securely and immediately access case evidence online.
Triage solutions
Quickly triage evidence and save valuable time.
Quickly triage Mac and Windows computers, mobile devices, and external drives for illicit content such as CSAM, usernames, and contacts in the field or the lab with automated insights so you can prioritize case workloads.
Partner with Magnet and let us help you transform your digital investigations.
Speak to one of our experts today.
