Magnet AXIOM Cyber 6.0: YARA Rules, Queued Collections, Dark Mode, and More!
The latest major release of Magnet AXIOM Cyber, version 6.0, is now available.
There are a lot of exciting improvements in this release of AXIOM Cyber—here are the top six:
- Support for YARA rules
- Queue remote collections
- Dark mode
- New Chrome extension for Google Workspace acquisitions
- New receipt and invoice classifier for Magnet.AI
- New and updated artifact support
If you haven’t tried AXIOM Cyber yet, there’s no better time than right now to request a free trial here.
Keep reading to learn more about each of these new features in AXIOM Cyber.
1. YARA Rule Processing
According to the 2022 State of Enterprise DFIR Report, Magnet Forensics, in collaboration with IDC, found that ransomware and malware infected endpoints were 40% of all cases dealt with by DFIR professionals surveyed in 2021.
Malicious threat actors are unrelenting as cyberattacks are increasing in frequency as well as sophistication. Incident Response handlers and DFIR examiners need a way to respond quickly to cyberattacks.
AXIOM Cyber 6.0 introduces YARA rule processing to accelerate incident response investigations.
YARA is a rule-based approach for identifying malware. Rules are created and often shared with the community on research blogs and threat feeds whenever a particularly nefarious exploit is discovered. These rules can then be ingested into a processing engine that scans evidence sets for matching results.
In AXIOM Cyber 6.0, you can now process evidence using YARA rules to identify matching files. A new artifact entry is created and enumerated per rule hit. Contextualize the rule hit within the suspicious file using a hex card so you can validate your findings quickly.
2. Queued Remote Collections
Sometimes you’ll know exactly what it is that you’re looking for on a target endpoint, a malicious file for example, but you’re unsure which endpoint—or endpoints—has been compromised. If you can’t afford to do a full acquisition of each endpoint, you need a quick and convenient way of acquiring data from multiple endpoints.
AXIOM Cyber 6.0 gives you the ability to create a queued list of target endpoints (up to 15) to acquire from using Targeted Locations. AXIOM Cyber will sequentially collect from each endpoint in the queue until the job is complete.
For added control and flexibility of the queued collection job, you can configure how AXIOM Cyber should proceed if an endpoint is unavailable: specify how long to wait, the number or retries as well as when to skip or re-prioritizing an endpoint to the bottom of the queue. This way when an endpoint isn’t available the collection process can still progress.
And once your job is done, data collected from each endpoint is conveniently consolidated into one case file making it easier for you to find what it is that you’re looking for across all of the endpoints collected.
3. Dark Mode
We know that you can spend hours upon hours staring at AXIOM Cyber diligently working through an investigation trying to piece together all the different items of evidence, often under an extreme amount of pressure.
Give your eyes a break and try out dark mode!
To turn on Dark Mode, simply go to Settings in AXIOM Cyber and under UI Theme choose Dark Mode. And don’t worry, if you prefer Light Mode, it hasn’t gone anywhere. You can choose whichever UI theme you prefer.
4. Acquire Google Workspace Data with a New Chrome Extension
In an effort to protect its users from a range of security threats, Google announced that it would block sign-ins from CEF-based apps, such as DFIR tooling. This presents a challenge for those who legitimately need access to Google data and have relied on CEF-based frameworks to acquire it.
AXIOM Cyber 6.0 introduces a new non-CEF method for businesses to acquire Google Workspace data from target accounts: the new Cloud Authenticator Chrome extension. Using this method to acquire Google data from the target account will not only be more reliable compared to CEF-based approaches of acquiring Google data with AXIOM Cyber, such as simple username and password authentication, it will also give you access to the highest level of data in the target account.
5. Receipt and Invoice Classifier for Magnet.AI
AXIOM Cyber 6.0 introduces a category classifier for Magnet.AI: Receipts and Invoices. Document alteration and fraud involving invoices or receipts diminishes the bottom line of a business and can potentially go unnoticed for long periods of time. Using the new Receipt/Invoice classifier, it’s easy to collect all pictures or PDFs that look like receipts or invoices.
Magnet.AI is a feature of AXIOM Cyber that will search your case data for pictures—and chats that may be indicative of sexual harassment—that contain in a particular category, documents for example or screen captures. If a picture contains content in a particular category, it’s tagged for later review in the Artifacts explorer.
Magnet.AI is equipped with OCR and optimized for extracting text from PDFs, scanned documents, or pictures of documents. You can view the extracted text using OCR preview card within the Details panel. Additionally, you can search the extracted text from files using the standard keyword searching capabilities of AXIOM Cyber.
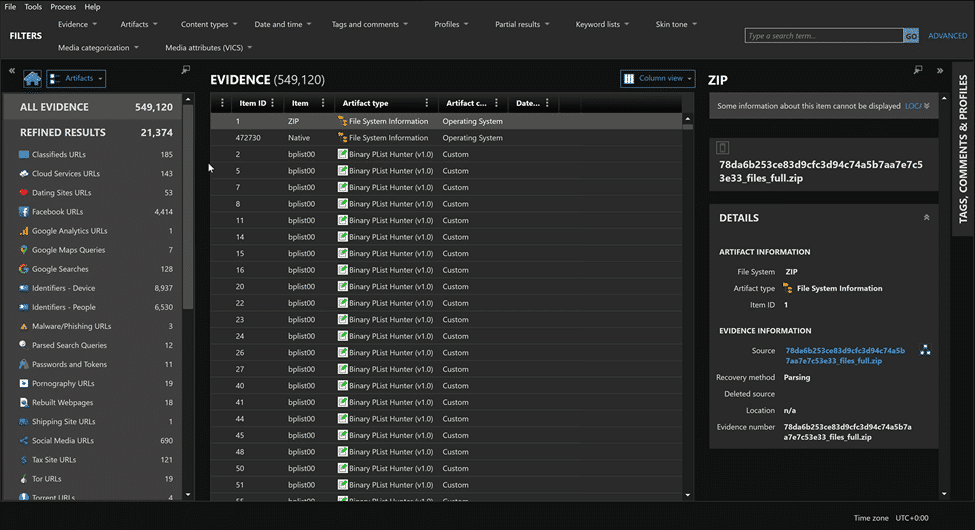
6. New and Updated Artifacts
As always, with every new release comes support for new artifacts as well as updated support for artifacts that may have changed over time. Apps and services are constantly changing, and the way that your DFIR tool parses and carves those artifacts needs to change just as fast. It’s one the reasons why Magnet Forensics is committed to delivering product updates monthly, not just two or three times a year.
One of the updated artifacts of particular interest is Outlook Email recovery from iOS, Android, and macOS. AXIOM Cyber now supports the HxStore format giving you the ability to recover emails from:
- Windows Mail app
- Outlook for Android
- Outlook for iOS
- Outlook for macOS
Here’s the full list of artifact support for AXIOM Cyber 6.0.
New Artifacts
- Outlook emails // macOS
Updated Artifacts
- Android SMS / MMS
- Apple Keychain
- Bitcoin Debug Logs
- Bluetooth Devices
- Chrome Logins
- Chrome Logins
- Cloud Passwords & Tokens
- Identifiers – People
- iMessage Messages
- Outlook Accounts
- Outlook Emails
- Photos Media Information
- Proton Mail
- Refined Results – All URL-based refined results
- Refined Results – Passwords & Tokens
- Slack Workspaces
- SMS / MMS
- Telegram Messages
- Telegram Users
- Videos
- WhatsApp Messages
- Windows Mail
Get Magnet AXIOM Cyber 6.0 Today!
If you’re already using AXIOM Cyber, download 6.0 over at the Customer Portal. If you want to try AXIOM Cyber for yourself, request a free trial today!
