Fighting CSAM With Magnet GRAYKEY
The online sexual exploitation of children has become increasingly prevalent in our society. According to the National Center for Missing and Exploited Children (NCMEC), there were 29.3 million reports of suspected child sexual exploitation in 2021 – the most ever reported in one year. Unfortunately, many child victims never receive justice because the crimes are neither reported, nor perpetrators caught. And with the growth of mobile device usage, the cat and mouse game between predators and law enforcement is even more complex. But how can we protect the vulnerable and seek justice in the digital age? The answer is not simple. However, law enforcement, internet and electronic service providers, and technology companies have come together to address the CSAM problem. And now, Magnet GRAYKEY has entered the fight to provide lawful access to mobile devices so examiners and investigators can extract the critical evidence they need to solve CSAM cases.
What is Child Sexual Abuse Material?
Child Sexual Abuse Material, commonly referred to as CSAM, is a term used by many to describe images, videos, written accounts, conversations, and other things that depict or describe sexual abuse and exploitation of a minor. Historically and legally, the term child pornography has been used to describe images and videos detailing child sexual abuse. However, that term doesn’t accurately capture what is occurring. The truth is, no matter what you call it, it is horrific.
What are the dangers of CSAM?
One of the most common CSAM types is images and videos. Not only does CSAM document victims’ exploitation and abuse, but when these files are shared across the internet, child victims suffer re-victimization each time the image of their sexual abuse is viewed. So, even if the abuser is found and charged, the CSAM likely lives on forever – a constant reminder of the victim’s suffering.
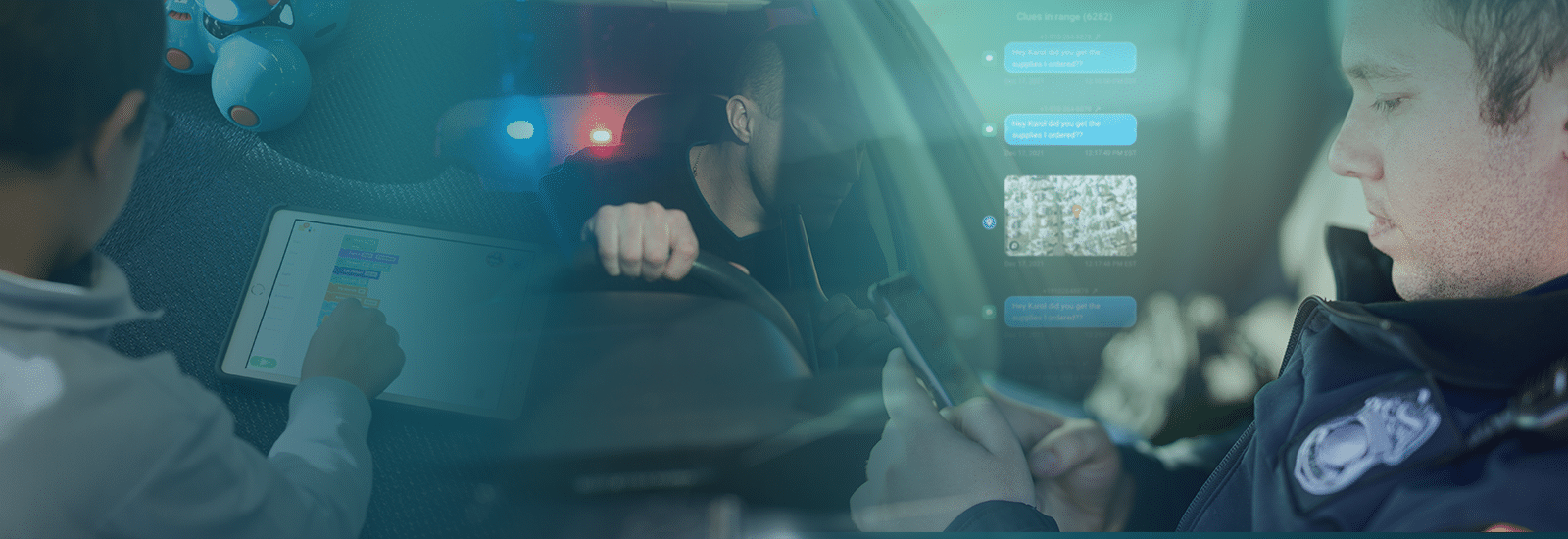
How can GRAYKEY help with CSAM investigations?
GRAYKEY is a mobile forensic tool that helps law enforcement agencies access and extracts encrypted or inaccessible data from mobile devices. There are 6.5 million smartphone users worldwide and the use of mobile devices in CSAM-related cases is on the rise. You get one step closer to prosecutors when you can access the data. With GRAYKEY, once you have a phone related to an investigation, you can look for the following artifacts to help you solve your case.
Multimedia
Photos and videos the most prevalent data sources for CSAM-related crimes. Finding this evidence helps confirm allegations, but these images can also help identify a child or the location where a victimized child may be. In some cases, images may even reveal additional victims.
Third-Party Applications
You can locate in-app messages or additional images and videos within these applications. Predators most often use these apps to communicate and groom their victims. Also, like-minded individuals preying on children will communicate with each other, sharing CSAM images, grooming strategies, and discussing their behavior.
Communication Data
In some instances, there may be communications between the child and offender. You may even find messages between multiple offenders.
Location Data
Location data is critical information, especially in instances where the child has met with an offender or if the child has been abducted. This data can often be correlated with other artifacts to help outline the order of events.
Internet Search History
Those who seek out CSAM images have common search terms they use to find the material they seek.
You gain an advantage when you have the proper tools to access and extract critical evidence from mobile devices. With GRAYKEY, you gain the ability to access the maximum amount of information possible. Make sure there is no safe place to hide for criminals who would victimize the most vulnerable among us.
