
Acquiring Publicly Available Instagram Information
Collecting data from Instagram via the Cloud directly in Magnet AXIOM and Magnet AXIOM Cyber can provide investigators with the most recent posts associated with a hashtag or user activity within public facing information. Acquiring data via the Cloud Module is particularly valuable because the information is collected immediately, whereas warrant returns, for example, provide dated information.
Get Started by Acquiring Public Instagram Activity Data
With AXIOM and AXIOM Cyber, examiners can extract publicly available Instagram information via a direct acquisition by using any Instagram or Facebook username and password to authenticate to Instagram. This credentialing provides access to data the authenticated user may see when logged in directly with a browser or mobile app.
The examiner can select the date range of the content to be collected, as seen below.
The default container for the acquired data is set for AFF4-L and can be changed to a standard .zip file by selecting EDIT.
Lastly, the examiner can choose to acquire the public facing data for a particular user account or the posts associated with a specified hash tag.
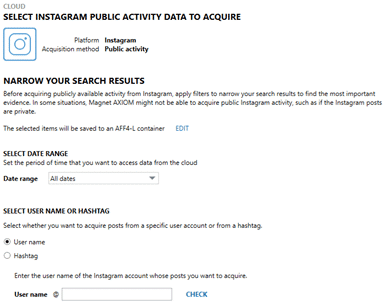
A targeted user account or user name can be obtained by searching on Instagram and selecting the account. The user name that needs to specified in AXIOM Process will be at the top of the user’s data that displays after selecting that account. After the user name is entered, AXIOM will “CHECK” to verify the account is valid and accessible with the credentials provided.
To collect data for a specified hashtag, AXIOM will also “CHECK” to verify data is available for download within the date range specified.
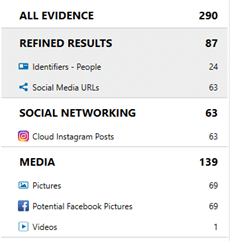
AXIOM Process will then parse the contents of the acquisition where the examiner can do further analysis in AXIOM Examine.
Being able to acquire Instagram data and artifacts both from the Cloud and a user’s devices is beneficial to generate a comprehensive overview of a user’s activity. Acquiring Cloud data will allow examiners to collect the most recent activity (especially, for example, if a phone is seized, Cloud account activity can continue on other devices), but artifacts on the device may still be present if data in the Cloud account or data is subsequently deleted.
User privacy settings will dictate what data is available for download from a particular user or hashtag. Users can change their post’s audience at any time and also “archive” data that will may reduce public access. Specifically, a user’s account settings must allow for public access to their activity regardless of hashtags included in posts.
You can upgrade to AXIOM in-product or over at the Customer Portal.
If you haven’t tried AXIOM or AXIOM Cyber yet, request a free trial here.
If you have any questions, please don’t hesitate to reach out directly via kim.bradley@magnetforensics.com.
Technical Advice Disclaimer
Magnet Forensics is dedicated to engaging with the DFIR community through our blogs and whitepapers. However, properly addressing technological issues often includes numerous variables that require independent assessment and strategies designed for each specific circumstance. Since Magnet Forensics cannot have complete insight into all variables involved in a specific situation, this blog/whitepaper is for informational purposes and should not be read as professional advice recommending techniques or technologies to address your specific situation. We do not accept responsibility for any omission, error, or inaccuracy in this blog/whitepaper or any action taken in reliance thereon.
