
Acquiring Publicly Available Facebook Information
Collecting data from Facebook via the Cloud directly in AXIOM can provide investigators with the most recent data associated with user profile and user activity, such as friends lists, public facing posts and comments. Acquiring data via the Cloud is particularly valuable because the information is collected immediately, whereas warrant returns, for example, provide dated information.
You can upgrade to AXIOM in-product or over at the Customer Portal.
If you haven’t tried AXIOM yet, request a free trial here.
Get Started by Acquiring Public Facebook Activity Data
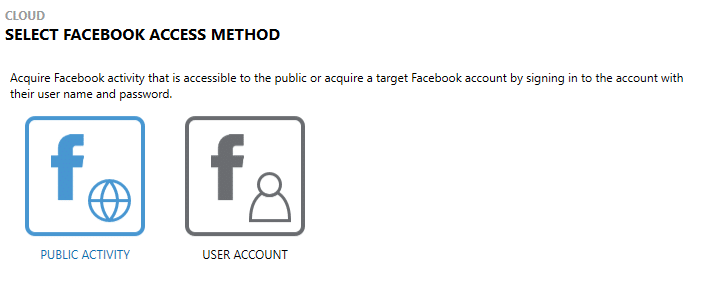
With AXIOM and AXIOM Cyber, examiners can extract publicly available Facebook information via a direct acquisition by using any Facebook username and password to authenticate to Facebook. This credentialing provides access to data the authenticated user may see when logged in directly with a browser or mobile app.
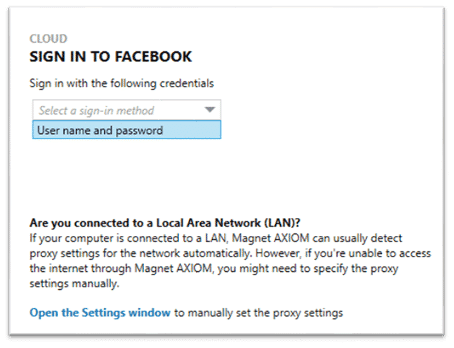
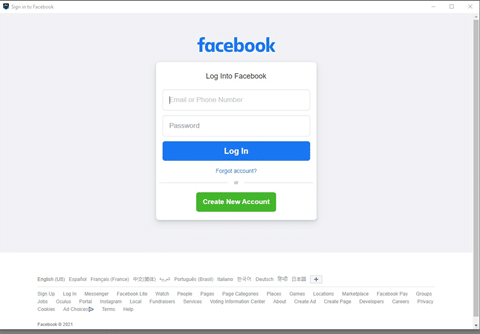
After a valid username and password have been provided, the examiner can select the date range of the content to be collected, as seen below.
The targeted Facebook account URL can be obtained by visiting the account in a browser and copying the associated URL. It will most likely be in the pattern of “https://www.facebook.com/[unique user ID]” or “https://www.facebook.com/username”. If data from the user referenced in the URL is available for acquisition, the options for content will display.
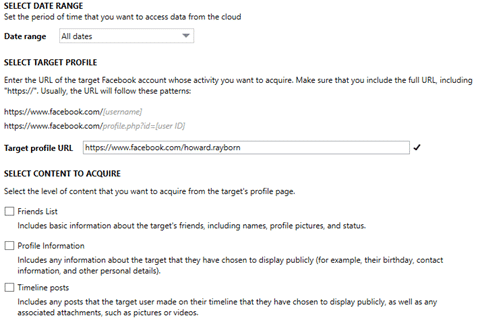
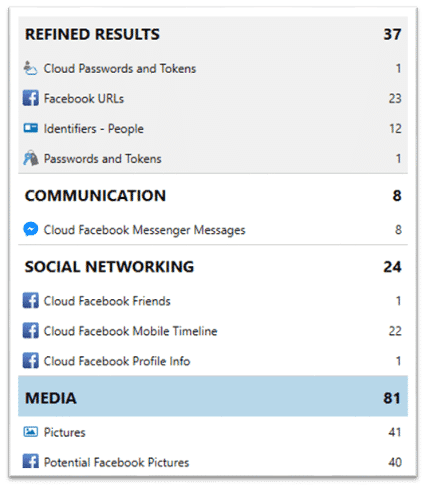
After selecting the content options, the data will be saved to an AFF4-L container. If users prefer using a standard .zip file, they can navigate to Settings to change from AFF4-L. AXIOM Process will then parse the contents of the extraction where the examiner can do further analysis in AXIOM Examine.
Being able to acquire Facebook data and artifacts both from the Cloud and a user’s devices is beneficial to generate a comprehensive overview of a user’s activity. Acquiring Cloud data will allow examiners to collect the most recent activity (especially, for example, if a phone is seized, Cloud account activity can continue on other devices), but artifacts on the device may still be present if data in the Cloud account is subsequently deleted.
It is important to note, though, that being able to locate acquire Facebook public activity data for the Facebook account of interest is dependent on the account’s privacy settings. Specifically, a user’s account settings must allow for public access to their activity.
If you have any questions, please don’t hesitate to reach out directly via kim.bradley@magnetforensics.com.
